Wireless LAN Maintenance and Troubleshooting Part 1
- Blog
- Networking
- Post
In this article, we’ll share with you all the important things you need to know to efficiently maintain and troubleshoot a wireless LAN. In this first part of the two part series, we will start off by discussing system maintenance on a WLC (Wireless Lan Controller), AP (Access Point), and WCS (Wireless Control System).
Then we’ll proceed to share with you a tested and proven troubleshooting model. We’ll also take up some common issues and their corresponding mitigation steps.
(Instructional video below provides a walkthrough of the steps contained in this article.)
Check existing code version
You can obtain the version of your existing code by using any of the following series of steps:
Through the Wireless LAN Controller:
- Login to the WLC web interface
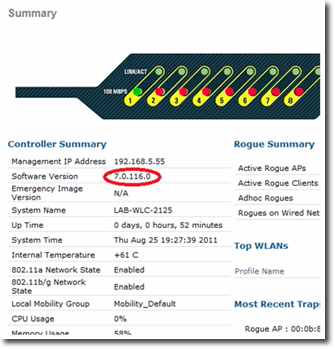
- Look for the software version number on the Summary page. This is what you should be looking for on the Summary page:
- Login to the WCS web interface
- Navigate to the Monitor tab and select Controller.
- Look for the software version number on the Summary page.
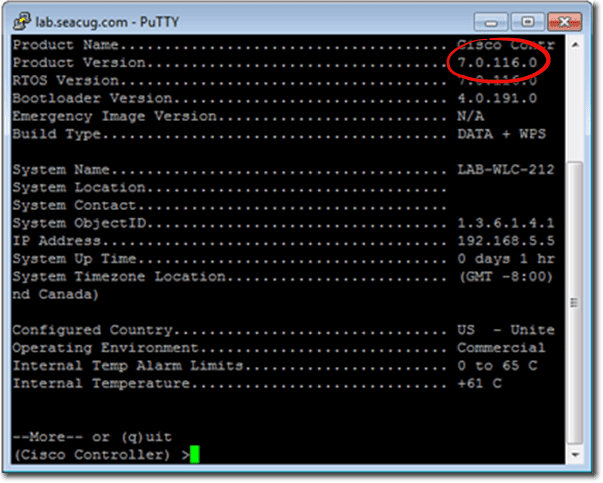
Through the command line:
- Login to whatever CLI program you wish to use (e.g. Telnet or SSH).
- Execute the show sysinfo command.
- Scroll to the output labeled Product Version and get the software version number from there.
Determine what version you can upgrade to
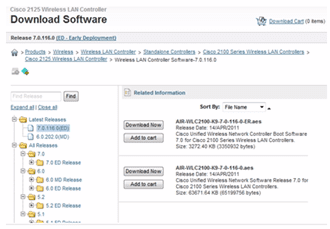
After knowing which version of the code you currently have, the next step is to determine what available version of the code is that you can upgrade to. This is done through www.cisco.com. Note that you can only download the appropriate code from there if you have both a cisco.com user ID and a valid Cisco SMARTnet service contract. If you have those two, then you can proceed as follows:
- Login to www.cisco.com, navigate to Support and go to Downloads.
- Search for the latest version for your particular controller model. Note that Cisco will limit you to download only device software that match your service contract.
- Save the file to your laptop, desktop or server.
- Obtain a TFTP server, which you will use in transferring the downloaded code from your computer to your controller. We recommend tftpd32 because it supports files greater than 32 MB. Some models can actually work with ftp but there are also some models that can’t, so tftpd32 is really the safest choice.
The Upgrade Process
We now go to the final step, which is the upgrading process itself. Again, there are three ways you can do this: through a command line interface, the WCS web interface, or the WLC web interface.
- Using a command line interface (CLI) – Although you may rarely use this, it still pays to know how to do things in a CLI. You’ll never know when things can go wrong and the command line will be all you have access to.Upgrading through the command line entails using the transfer download command set, wherein you’ll be asked for the name of the file you want to transfer, the location of the tftp server, the path of the file, and so on. Once everything’s ready, you then use the transfer download start command to initiate the upgrade process. When the file transfer completes, just follow the instructions on the screen.
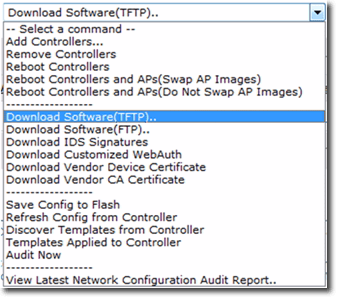
- Using the WCS web interface – Barring any hitches, the WCS web interface is the best option because, in addition to having a graphical user interface, it already comes with a built-in TFTP server.Once you’re inside the WCS web interface, expand the Configure drop-down menu and select Controller. Next, click the check box next to the controller, select Download Software, and click Go. Note that, when we say ‘download’ in this context, we mean putting a file on the controller. On the other hand, when we say ‘upload’, we mean pushing a file from the controller. After that, just follow the instructions on the screen.
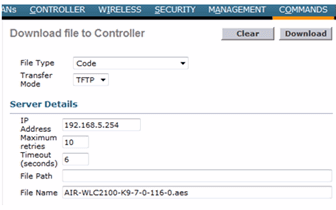
Using the WLC web interface – If you want to use the WLC web interface in performing the upgrade, make sure you activate the TFTP server first. When it’s ready, go to the WLC web interface and go to Commands and enter/select the following settings:
- File type: choose Code
- Transfer mode: choose between TFTP or FTP
- IP Address: Enter the TFTP server’s IP address
- File Path: Enter the file path and don’t forget to include ‘/’.
- File name: Enter the file name, which should include the file name extension .aes.
When you’re done, click the Download button. You can monitor the ensuing process through the TFTP server or the Wireless LAN Controller console. Configuration backup/restore Whenever you arrive at an equipment configuration that lets your wireless system run smoothly, it’s advisable to perform a backup on that configuration. That way, you can quickly and easily restore it in the future in the event that that particular equipment’s configuration somehow gets messed up.
Backing up and restoring is very similar to the process of uploading and downloading code. The main difference is that, instead of dealing with a code file type, you’ll be dealing with configuration file types. So, for example, in the WLC web interface, instead of selecting Code from the File Type drop-down list, you need to select Configuration.
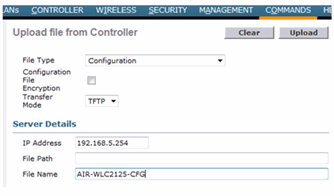
Configuration backup using the WLC web interface:
- Activate your TFTP server.
- In the WLC web interface, navigate to the Commands menu and select Upload File. Then enter/select the following settings:
- File Type: choose Configuration
- Transfer mode: choose between TFTP and FTP
- IP Address: Enter the TFTP server’s IP address
- File Path: Enter the file path and don’t forget to include ‘/’.
- File name: Enter the file name. For good practice, we recommend you attach a ‘cfg’ at the end of your file name, just so you can easily recognize it as a configuration file. When you’re done, click the Upload button. You can monitor the ensuing process through the TFTP server or the Wireless LAN Controller console.
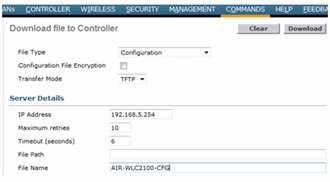
Configuration restore using the WLC web interface:
- Activate your TFTP server.
- In the WLC web interface, navigate to the Commands menu and select Download File. Then enter/select the following settings:
- File Type: choose Configuration
- Transfer mode: choose between TFTP and FTP
- IP Address: Enter the TFTP server’s IP address
- File Path: Enter the file path and don’t forget to include ‘/’.
- File name: Enter the file name.
When you’re done, click the Download button. You can monitor the ensuing process through the TFTP server or the Wireless LAN Controller console
Alarms and system monitoring
Both the WLC and the WCS are equipped with alarms and monitoring features. However, because the main purpose of the WLC is really designed for supervising and configuring access points, it doesn’t have as many alarms and system monitoring features as the WCS.
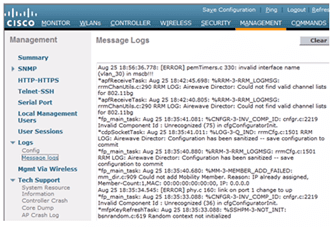
WLC Alarms and system monitoring – The alarms on the WLC come only in the form of crash logs, message logs, core dumps, AP crash logs, and other log outputs, which are accessible via the Management menu (at the top of the screen).
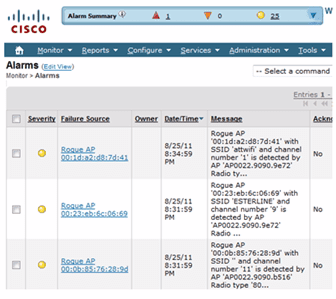
WLC monitoring functions, on the other hand, are mostly available under the Monitor menu and they deliver snapshots of information such as the controller’s health, access point status, wireless system statistics, clients that are currently active, and a rogue access point summary. WCS alarms and system monitoring – Here you can find a more extensive selection of alarm functions. For instance, it has a more detailed log output, which is available via the Alarms section under the Monitor menu. In the Alarms section, you may see a list of rogue access points along with relevant information such as their MAC address, name, SSID, channel, and many others.
WCS monitoring functions, on the other hand, are immediately available on the WCS home screen dashboard. They are shown on tabs like:
- General – Talks about access points, radios, clients, Wireless LAN Controllers, etc.
- Client – Displays the client count, the traffic being generated by clients, protocols in use, etc.
- Security – Talks about attacks, rogues, and status information
- There are also advanced tabs like Mesh, Clean Air, and ContextAware.
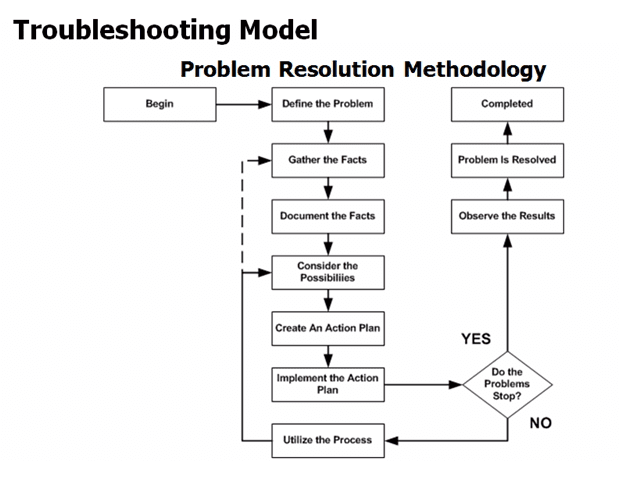
Troubleshooting Model
In order to deal with wireless issues effectively and efficiently, you need to approach each problem with a deliberate, thought-out methodology. This is where a troubleshooting model comes into play. The 8-point model outlined below is adopted from some of Cisco’s documentation and educational pursuits and is very applicable in the wireless environment.
The Troubleshooting Model:
- Define the Problem
- Gather the Facts
- Document the Facts
- Consider the Possibilities
- Create an Action Plan
- Implement the Action Plan
- Repeat Until Resolution
- Document the Solution
Define the Problem When a user complains that “the network’s slow”, you need to make sure that the network is really the problem, and it’s not because somebody is just downloading a large file or that the complainant’s PC is actually the one that’s problematic. And even if the problem is really the network, you still need to pin down exactly where the problem lies before you can proceed to the next step.
Gather the Facts Ask as many relevant questions as you need. Try to find out for example: when the problem started occurring; whether the problem is broad or localized; whether other users are experiencing the same problem; etc.
Document the Facts As you proceed with your investigation, record all the facts. This can be helpful when you start considering the possibilities. If you won’t be able to recall all the relevant information when it’s time for the next troubleshooting step, you could end up unnecessarily repeating steps you’ve already taken.
Consider the Possibilities Based on the facts collected, try to analyze and see what the possible causes may be. This is where you’ll be able to realize the benefits of good documentation. When it’s time to consider the possibilities you will be able to do so from an informed perspective by looking at the documented data.
Create an Action Plan If one possible cause stands out, draw up an action plan to tackle that one. It’s always best to tackle one possible cause at a time.
Repeat Until Resolution If your action plan worked, then you’re done. You can proceed to the next step. However, if the problem still persists, go back to considering the possibilities.
Document the Solution This part is useful because you can use the documented solution in case a similar complaint is brought up in the future.
Here are those steps again, presented in a flow chart. Notice how it may be necessary to go back to the drawing boards and gather facts which may not have been collected before.
Common Issues and Mitigation Steps While there are certainly a lot of wireless issues out there, the ones we’ve featured below are some of the most common. We’ve grouped them in terms of client issues, access point/WLAN issues, and controller issues. Client issues
Of all three groups of issues, client issues are probably the most common. This is because end users are mostly non-technical people and hence may not know how to resolve simple problems by themselves. Here are some of those issues along with the possible causes and their corresponding solutions. Issue: Client cannot connect to the AP/WLAN Possible causes and their corresponding solutions:
- WLAN is disabled on the WLC: Log into the WLC, select the WLAN menu item, select the WLAN, and ensure that the Enable check box is activated.
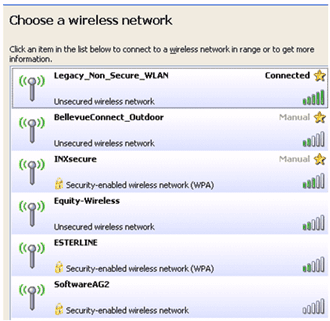
- SSID is mismatched: Ensure that the SSID name is spelled correctly. Remember that it is case-sensitive.
- Security key is incorrect: Re-enter the key.
- Signal from AP is weak: Use a client software to determine the signal strength and move to an area where the signal is strong.
- Outdated or corrupt drivers: Get the latest drivers from the wireless adapter’s manufacturer or perform an OS update.
- RF interference: Remove the device that may be causing the interference; use 802.11a; or simply relocate.
Issue: Client is not receiving an IP address Possible causes and their corresponding solutions:
- DHCP server is unreachable: Investigate network issues by inspecting VLAN settings, network settings, and WLC settings.
- DHCP request timed out: On a Windows client, issue the ipconfig release/renew command.
- DHCP server is offline: Re-enable DHCP server or create a new one.
Access Point/WLAN issues Issue: No clients are associating with the AP 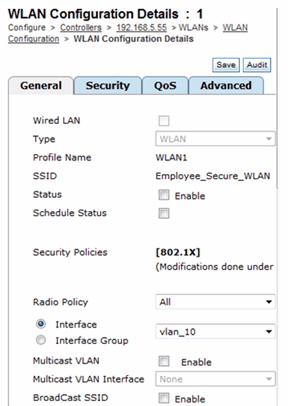
Possible causes and their corresponding solutions:
- SSID is not broadcasted: Make sure the SSID is set to enable broadcast or the users have the correct SSID string.
- WLAN is disabled: Log into the WLC, select the WLAN menu item, select the WLAN, and ensure that the Enable check box is activated.
- Authentication failure: Check the RADIUS server
Issue: Clients are complaining about performance Possible causes and their corresponding solutions:
- Saturated AP: Verify the number of clients on the affected AP and if you think it exceeds the number that that AP is capable of serving, set limits to the number of clients that can associate with that AP.
- AP Software is Corrupted: Reimage the AP using the WLC/WCS and try again.
- AP radio is down: Check the radio settings
- AP is inoperative: Replace the broken AP
Controller issues
Issue: Traffic from WLAN unable to reach wired network through controller Possible causes and their corresponding solutions:
- Misconfigured VLAN settings: Check that the correct VLAN ID is configured on all devices, verify WLC 802.1Q trunk.
- Incorrect physical port settings on Controller: Check that the port connected to the wired network is identified and configured correctly.
Like we said earlier, this is by no means an exhaustive list. There are certainly more wireless issues out there. But we hope this list can help you get a feel of the kind of issues you may later on encounter.
Summary
This concludes part 1 of this two-part series. In part 2 we will discuss some tools for problem identification and resolution System maintenance typically involves any of the following tasks: upgrading system code, backing up or restoring configuration, and using alarms and system monitoring tools. There are a couple of steps you need to go through to achieve that, which we will walk you through.