What Is Windows Defender System Guard in the Fall Creators Update?
In this Ask the Admin, I’ll explain how Windows Defender System Guard reorganizes existing security defenses.
Windows Defender System Guard in the Fall Creators Update is a new label for a set of technologies designed to ensure that the system can’t be compromised or if it is, notify the user. Microsoft says it has three goals for System Guard:
- Protect and maintain the integrity of the system as it starts up
- Protect and maintain the integrity of the system after it’s running
- Validate that system integrity has truly been maintained through local and remote attestation
It is important to focus on maintaining system integrity because if Windows is compromised, then all other security defenses will likely fail. System Guard isn’t compromised of new features but instead brings together existing security defenses. Microsoft hopes this will make it easier to invest in security and make further improvements in the next major Windows release, which is expected in spring 2018.
Hardware-based root of trust, or Secure Boot as Microsoft refers to it, was introduced in Windows 8 and helps protect the OS during startup, ensuring that a malicious bootloader cannot start before Windows loads. Secure Platform Boot then ensures that as Windows loads, files and drivers are signed. Finally, antivirus is started to check third-party drivers.
See Enabling Secure Boot in Windows 8 and Windows Server 2012 to check if Secure Boot is enabled on your system.
Virtualization-based security (VBS), which was introduced in Windows 10 to isolate critical parts of the OS using containers, has been renamed to the Windows Defender System Guard container. In addition to enabling Credential Guard and Device Guard, for protecting domain credentials and application control policies respectively, System Guard container enables other technologies, including Virtual TPM and parts of Exploit Guard.
System Guard can verify the integrity of the OS while it is running. In an ideal world, we’d be able to trust the security defenses that I’ve described to protect the OS and assume that Windows hasn’t been compromised. But we should never assume that a system hasn’t been breached and System Guard aims to determine that a system is healthy or notify the user if it is not.
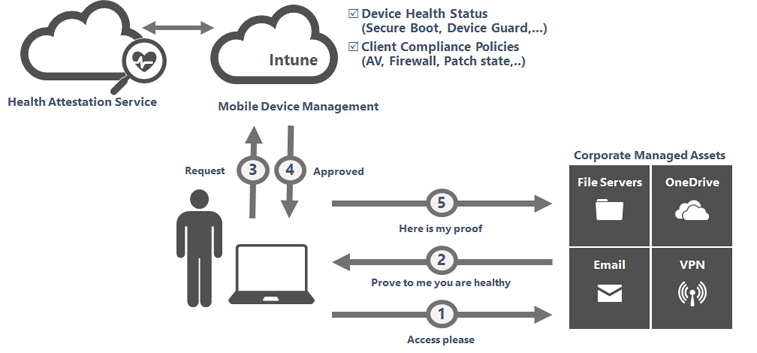
By taking a set of integrity measurements as the system boots and storing them in a TPM to prevent tampering, System Guard can handover this data to management systems, like Intune or System Center Configuration Manager, and access blocked to resources if System Guard determines there’s a problem with the system’s integrity. Device Health Attestation (DHA) isn’t enabled by default in Windows 10 and is a reactive security defense. It won’t stop Windows booting if System Guard identifies a problem. But it can be used to block a device’s access to sensitive network resources.
In addition to a Mobile Device Management (MDM) service, like Intune, DHA requires a Health Attestation Service server, which can be either hosted on Windows Server 2016, a free Microsoft-managed DHA service, or a virtual host in Microsoft Azure. For more detailed information on Windows 10 DHA, see Microsoft’s website here.
Windows Defender System Guard is more a reorganization of existing technologies than something completely new but the groundwork that Microsoft has done in the Fall Creators Update is about simplifying Windows to make it easier to build new defenses into the operating system. But not only that, it helps Microsoft streamline its message around security.