In this Ask the Admin, I’ll look at the technical details of how Windows Defender Exploit Guard (WDEG) will replace the Enhanced Mitigation Experience Toolkit (EMET) in Windows 10.
The Fall Creators Update is bringing additional security features and changes for enterprise customers, including improvements to Windows Defender Security Center and Advanced Threat Protection (ATP). Windows Defender Application Guard will allow administrators to isolate untrusted websites in Edge using hardware virtualization and Exploit Guard replaces EMET.
Microsoft’s EMET, which can be used to harden the security of apps like Internet Explorer, was retired at the end of last year. While each new version of EMET protected against exploits at the time of release, without customers having to wait for the next version of Windows, hackers found ways to bypass EMET because the mitigations were not durable and often worked in ways that caused OS and app stability issues. So, Microsoft decided to retire EMET to focus on providing a better experience in Windows 10.
Because Windows 10 is Software-as-a-Service, the latest defense mechanisms can be integrated directly into the OS. It is shipped to customers much faster than in previous versions of Windows, which received feature upgrades only once every 3-4 years. EMET will be supported through to January 2018 for customers that do not have immediate plans to upgrade to Windows 10.
Windows Defender Exploit Guard
WDEG is a solution in the Windows 10 Fall Creators Update for managing the existing mitigations that were in previous versions of Windows 10. And it adds new and improved features that were previously part of EMET, including:
- Apply Control Flow Guard (CFG) mitigations to legacy apps without recompiling them
- Audit mode for EMET and existing Windows 10 mitigations
- New mitigations
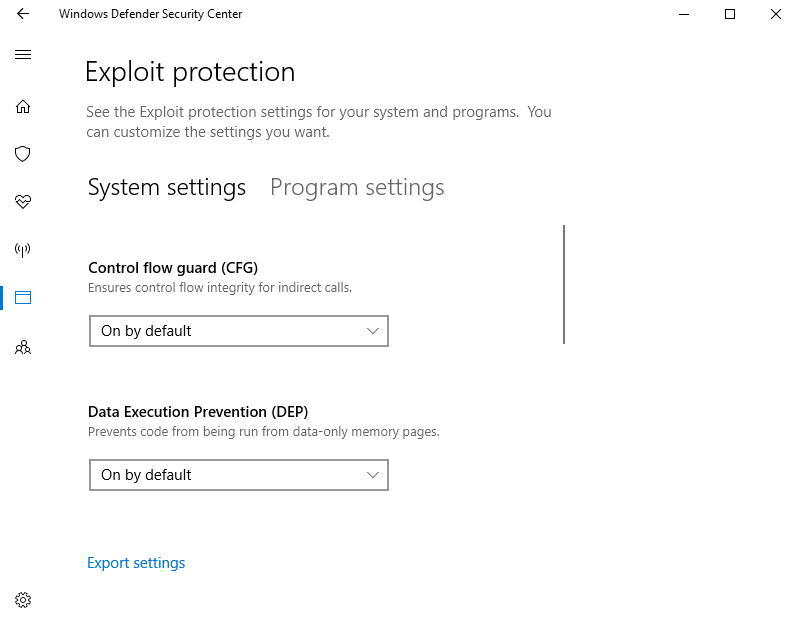
WDEG settings can be accessed in the Fall Creators Update under Apps and browser control in the Windows Defender Security Center, which has been updated for this release. WDEG also integrates with Windows Defender ATP showing WDEG events on the Windows Defender ATP timeline.
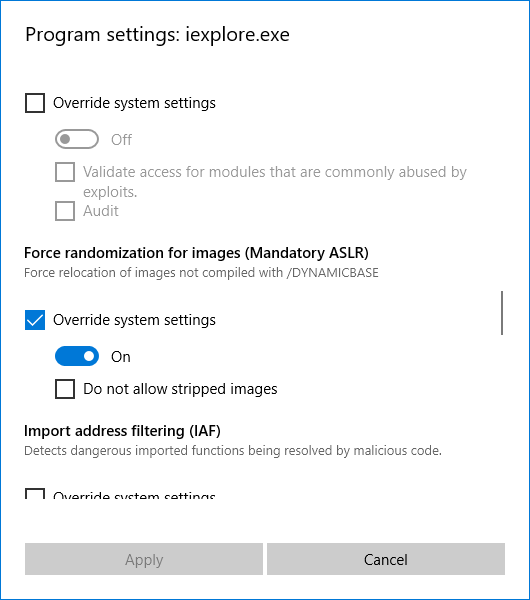
The controls for WDEG are separated into system and program settings. Program settings allow administrators to target individual applications with a wide range of mitigation techniques. Each mitigation can be run in audit mode if required. You can use Windows Defender Security Center to export WDEG settings for use in the new Use a common set of exploit protection settings Group Policy setting under Computer Configuration > Windows Components > Windows Defender Exploit Guard > Exploit Protection. Settings can also be exported using the Get-ProcessMitigation PowerShell cmdlet.
Security Band-Aid
Operating systems like Chrome OS that are built from the ground up with security in mind are naturally quite resistant to attack. Windows is targeted because of its widespread use in the enterprise but it is also more easily hacked because it has a large attack surface thanks to legacy win32 support. It is not locked down out-of-the-box.
Enterprises that want the flexibility to run legacy desktop apps and the management and deployment features that its infrastructures are designed for, should think about upgrading to Windows 10 to benefit from the additional security that Microsoft is integrating into the OS.



