In this Ask the Admin, I’ll show you how to be sure the source media you use to install software in your business hasn’t been tampered with.
In a previous Ask the Admin, I talked about the clean source principle, which states that a system can be dependent on a higher trust system but not on a lower trust system. Part of implementing the principle is to determine the security dependencies systems have on each other, including servers, users, hardware, and management tools. Server and PC setup starts with the installation source, such as a downloaded file or physical media.
If the media used to install or update software has been modified by a malicious actor, then the device on which the software is installed will be compromised from the get-go, along with any systems dependent on it. So, it’s important to understand that installation media is also a security dependency.

It’s best practice to validate the integrity of media before it’s used. Once the integrity has been confirmed, the media should be stored in a location that is restricted to systems with the same or higher level of trust as the devices where the software will be installed. For example, application installers should be protected against write access from Internet-connected hosts.
Certutil and Sigcheck
It might seem like overkill but you should check the validity of every installer file you download rather than assuming you have a genuine copy. Files could be downloaded from a site that appears to be the vendor’s but is, in fact, being diverted to a malicious server. This is especially important for mission-critical systems, such as Windows Server.
In the steps below, I’ll show you how to generate and compare the hash value of two files. A file’s hash value is a fixed-length number that uniquely identifies the file. You’ll download the file on two separate devices and generate hashes for each file. If the hash value is the same on both files, you can be reasonably sure that the file is genuine.
- Download the installer file on two separate devices that are isolated from each other. I.e. it is not connected to the same network or part of the same workgroup or domain. The devices should be connected to different Internet connections.
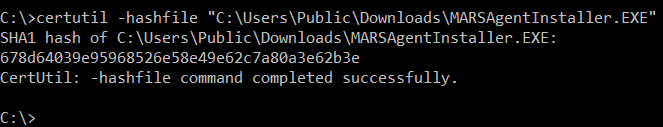
- Use certutil, a command-line tool built into Windows, to generate a hash for the file on both devices.
certutil -hashfile "C:\Users\Public\Downloads\MARSAgentInstaller.EXE"
It might sound like a pain to find two devices connected to different Internet connections but you could download the file at home and work and then compare the hash values.
It’s also worth checking the file’s digital signature. Not all software is digitally signed. But a signed installer package helps you to validate the file’s authenticity and integrity. To check the details of a file’s certificate, download Microsoft’s SysInternals sigcheck command-line tool. The command below will display basic information about the file’s digital signature.
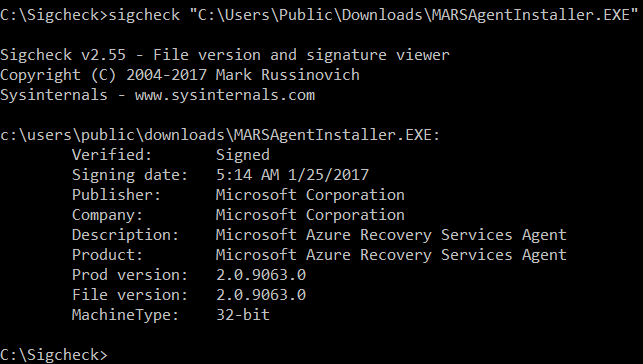
sigcheck "C:\Users\Public\Downloads\MARSAgentInstaller.EXE"
In this Ask the Admin, I showed you how to check the integrity of installation media using certutil and sigcheck.




