intune
- Blog
- intune

What Is Microsoft Entra ID Conditional Access? (And How To Use It)
Conditional Access is a security feature that allows organizations to control corporate resource access based on certain conditions. Common reasons for utilizing this technology include the enforcement of multifactor authentication (MFA), requiring stronger authentication measures during authentication, and more. Learn more about how to use Conditional Access to protect your data and devices. What is...
Last Update: Apr 01, 2024
- Oct 23, 2018
-
LATEST
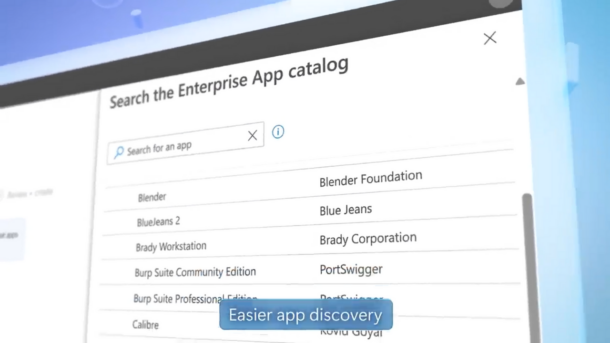
Streamline Application Deployment with Microsoft Intune Enterprise App Management
- Feb 13, 2024
-
Packaging and rolling out third-party applications to Windows endpoints has traditionally been a daunting task. It often involves a significant amount of testing and trial and error, and it can become a major time sink for IT Professionals. Recognizing this challenge, Microsoft announced a solution at its Ignite conference – a service set to make…

How to Automatically Hybrid Azure AD Join and Intune Enroll PCs
Last Update: Jul 17, 2023
- Mar 29, 2021
-
On-premises Active Directory domain-joined PCs have typically been managed with tools such as Group Policy. At larger scales, you may have Configuration Manager or third-party tools. The availability of Intune (part of Endpoint Manager) in Microsoft 365 subscriptions such as Business Premium and E3 has opened up an alternative. The benefit many are seeing over…

Implementing Access Controls using Microsoft Intune
- Jun 28, 2023
-
Implementing identity and access management processes is an effective way to protect sensitive corporate data. It allows organizations to regulate user access and prevent instances of identity theft, data breaches, and unauthorized access to confidential corporate information. In this article, we’ll detail how organizations can significantly minimize their exposure by controlling access privileges with Microsoft…

How to Add Microsoft Store Apps to Intune
- May 05, 2023
-
Microsoft has recently unveiled the Intune Microsoft Store repository integration, which is intended to replace the current Microsoft Store for Business integration with Intune and provide a more consumer-like experience for employees. Microsoft has also released the WinGet Windows Package Manager, which allows IT pros to manage apps and updates through the Microsoft Store repository…

How to Package and Deploy Windows Applications with Intune
Last Update: Aug 31, 2022
- Mar 24, 2021
-
Intune Administrators can deploy, make optionally available, or uninstall Win32 apps with the help of Windows 10’s Intune Management Extension (IME). The IME is a service installed on Windows 10 that acts as the engine to execute these actions and, additionally, PowerShell scripts (which were originally its only purpose). Win32 apps in the context of…

Windows Autopilot Deployment: A Step-by-Step Guide
Last Update: Aug 06, 2022
- Jul 29, 2022
-
Windows Autopilot is a new Microsoft tool that IT pros can use to pre-configure, reset, or repurpose Windows devices. It’s a great tool to automate the process of deploying Windows devices in an organization. In this Windows Autopilot deployment step-by-step guide, we’ll explain how to get started with Windows Autopilot and set up new devices…

How to Control Intune Enrollment with Enrollment Restrictions
- Apr 06, 2021
-
Enrollment restrictions are sets of rules assigned to Azure AD groups. There are two types of enrollment restrictions: device type and device limit.

Best Practices for Deploying BitLocker with Intune
- Mar 15, 2021
-
To protect data at rest on your Intune-managed Windows devices, BitLocker disk encryption can be applied automatically using the BitLocker CSP. If you are deploying devices with Autopilot, this will also allow you to encrypt them at the time of deployment. Existing devices will be encrypted as soon as the device checks in with Intune…

Microsoft Endpoint Manager’s Updates Aim to Simplify Mobile Device Management Policy Creation
- Mar 11, 2021
-
Rolling out in public preview early February 2021, Microsoft is adding a new feature to its Endpoint Manager (MEM) solution called settings catalog.







