Sponsored: Delegating Access in Active Directory
Editor’s Note: This blog post is the third in a four-part blog series from Adaxes.
Delegating access to Active Directory (AD) usually involves deciding which permissions to assign users so that they can perform a restricted set of tasks. However, providing access to AD also requires you to think about the appropriate management tool and user interface.
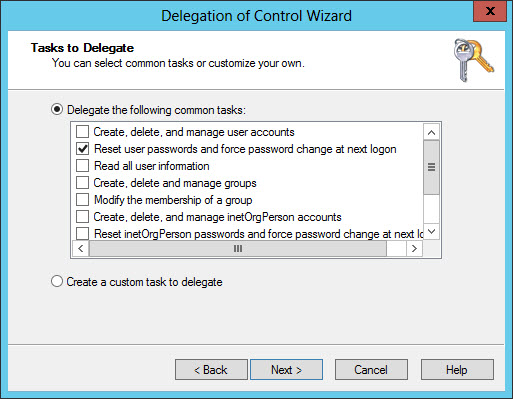
A well-designed Organizational Unit (OU) structure lets IT assign permissions and Group Policy Objects (GPOs) to different sets of AD objects. For example, you might want to allow Help Desk users to reset user passwords and unlock accounts, but not to modify the AD schema. AD permissions can be assigned manually or using the Delegation of Control Wizard, which has a built-in list of common tasks that make it easy to assign the necessary rights.
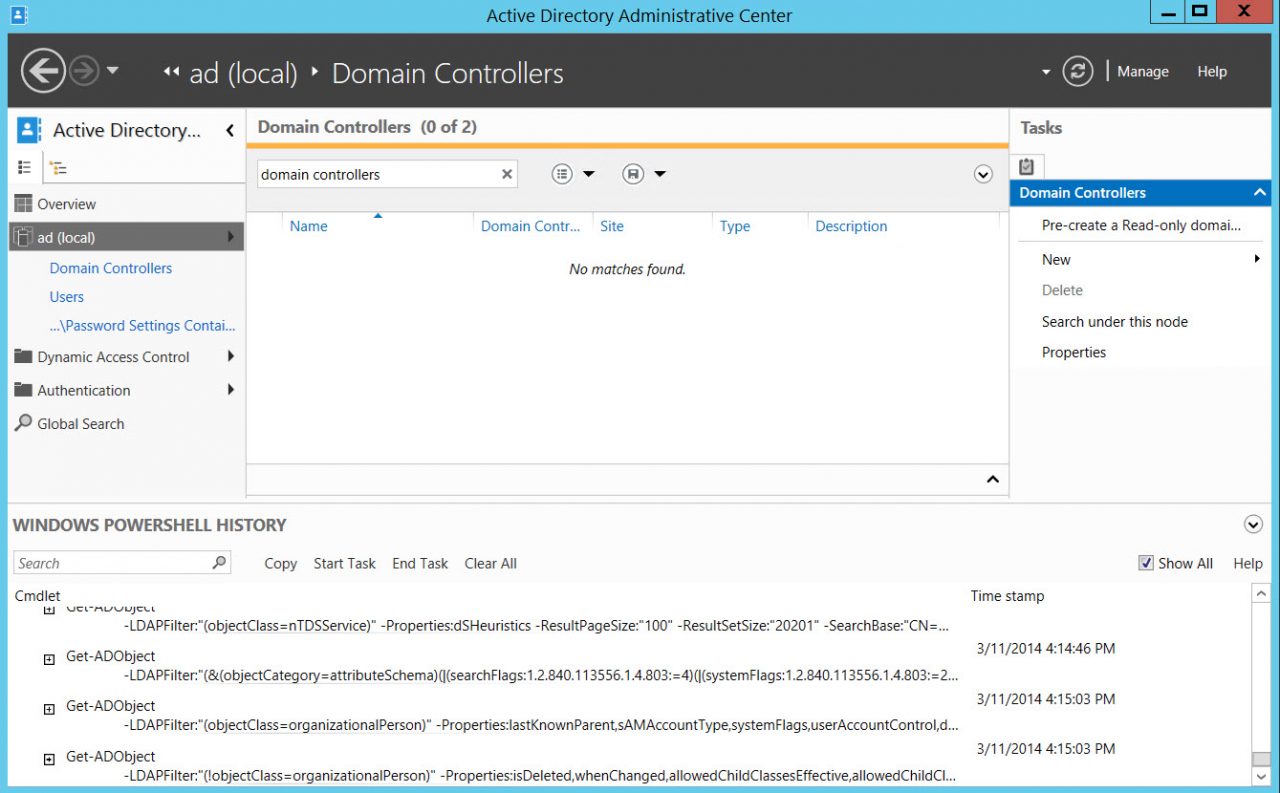
Windows Server’s out-of-the-box advanced tooling, such the Active Directory Users and Computers (ADUC) management console, has never been that easy to work with or suitable for non-technical users. It’s possible to customize the management consoles (MMCs) to a limited extent, but not enough to make them user friendly. Microsoft recognizes this, and in Windows Server 2008 R2 introduced the Active Directory Administrative Center (ADAC), which aimed to provide an enhanced management experience and a better graphical interface using data-driven and task-oriented navigation.
If none of Microsoft’s solutions are a good fit for your purposes, there’s always the option to create your own management console based on PowerShell or other command-line tools. If you have developers in-house, they could be tasked with creating MMC snap-ins to meet your requirements. Additionally, TaskPads can be added to custom MMCs without any programming knowledge.
See Create Custom MMC Consoles for Managing Windows Server and Delegate Permission to Reset AD User Account Passwords on the Petri IT Knowledgebase for more information about customizing MMC consoles and using the Delegation of Control Wizard.
But the solutions mentioned above require a considerable up-front investment and need to be maintained. There’s also the question of how to distribute these tools to users. Third-party AD administration tools, such as Softerra Adaxes, provide different web interfaces for managing AD depending on user needs. There are separate web interfaces for IT administrators, Help Desk staff, and user self-service. These interfaces can be customized so that IT can determine how AD objects are displayed, create custom forms for object creation and editing, and enable or disable interface components.
Adaxes makes it easy for users to modify their own personal data, search the directory, and perform any other tasks for which they have permission. Self-service password resets can also be performed, and is protected by a series of security measures, including challenge response questions and SMS verification, to ensure that malicious users can’t reset passwords.
For IT staff, the web interface provides access to all administrative tasks, assuming users have the necessary permissions, and is easier to use than Microsoft’s administration tools. Users can identify AD objects and add them to their favorites for quick access later. Advanced search helps to find objects using filters, and unlike ADUC, Adaxes includes built-in reporting that can be used to find information quickly. The Help Desk web interface provides a subset of features available in the administrators’ UI, allowing Help Desk staff to focus on the task at hand.
As an identity management service for systems and applications, it’s important to keep AD secure and up-to-date so that it can provide true value and protect your company’s assets. Adaxes offers a solution that gives everyone the access they need to the directory so that it can be properly maintained and secured.




