How to Shadow a Remote Desktop session in Windows Server 2012 R2
How can I use shadowing during a Remote Desktop session in WS2012 R2?
Windows Server 2012 R2 reinstates Remote Desktop shadowing so that administrators can view a user’s session when they are connected to a Remote Desktop. Due to some changes in how Remote Desktop worked in Windows Server 2012, shadowing was removed from the feature stack. By popular demand, shadowing is back in Windows Server 2012 R2 and can be found in Server Manager. Only administrators can shadow Remote Desktop sessions, and the Remote Desktop Session Host must be part of an Active Directory domain.
RDS Shadowing in Windows Server 2012 R2
You can shadow a Remote Desktop session either by specifying the /shadow switch from the mstsc command like, or from Server Manager.
- Open Server Manager in Windows Server 2012 R2 from the Start screen, or by clicking the icon on the desktop Taskbar.
- Click the Remote Desktop Services and then Collections in the left pane of Server Manager.
- Under Connections in the bottom right of Server Manager, right-click the connection that you want to shadow and select Shadow from the menu.
In the Shadow dialog box you can choose to connect with View or Control permission and decide whether the user needs to give their consent. Alternatively, you can use the following command line to shadow a session:
mstsc.exe /shadow:sessionID /control /noConsentPrompt
The /control and /noConsentPrompt switches are optional and correspond to the settings available in the Shadow GUI dialog seen in Server Manager.
Shadowing Permissions
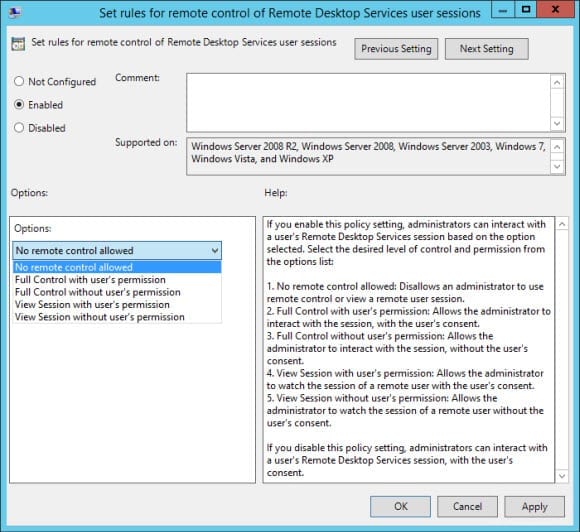
By default, Windows is configured such that users must give consent for an administrator to shadow a Remote Desktop session. This behavior can be overridden by setting the Set rules for remote control of Remote Desktop Services user sessions Group Policy setting under Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Connections. The same setting also appears under User Configuration.