Resisting Business Email Compromise Attacks on Office 365 Users
Some Security FUD About an Undocumented API
Last week I discussed how to use the Office 365 edition of Microsoft Cloud App Security (CAS) to gain greater insight into the security profile of an Office 365 tenant. If you already have Office 365 E5 subscriptions, using CAS is a no-brainer because it is included in your plan. If not, CAS is available as an add-on for $36/user/year and all accounts in the tenant need to be licensed to make the CAS analytics effective.
Since I wrote the article, several people have asked me about the “undocumented” API for Outlook mailbox activity reported in a blog written by a security forensics company called CloudStrike on June 18. Apparently, the security community discovered the new API through a video posted by the Anonymous hackers on June 8 revealing an API called Activities. Different security commentators took up the story to create some hype (here’s an example). Most of what I read was good old-fashioned FUD.
Activities Are Recorded by Office 365
Let’s consider what’s going on here. Microsoft has been quite clear that it gathers information about user activities within Office 365. Tenants can control whether administrators can search the audit log, but the same article makes it clear that “If you turn off audit log search in Office 365, you can still use the Office 365 Management Activity API to access auditing data for your organization.”
In other words, disabling the audit log search doesn’t stop Microsoft gathering activity information about what happens in a tenant and populating the Office 365 audit log. That information is available through the Management Activity API. Security products created by ISVs use the API to collect and analyze activity information when authorized by tenants.
Although they use the same data, ISVs compete with Microsoft with lower costs and some different functionality (like identifying Office 365 accounts with compromised passwords).
Telemetry
It’s also the case that Microsoft gathers a lot of telemetry data about how people use Office 365 apps. Microsoft uses their telemetry to find and fix problems, to understand what the most heavily used features are, and as a guide for future development. The data ends up in the Microsoft Graph. Some say that this is evidence that Microsoft spies on what people do inside Office 365. If so, it’s the same kind of thing that power companies do when they monitor the delivery of an electricity supply to a house.
The Activity API that all the fuss is about is part of the Outlook API. I bet the reason why Activities are not exposed in the same way as the other parts of the Outlook API is that the use is predominantly internal (telemetry).
Resisting Business Email Compromise Attacks
The more pertinent question is whether the data exposed through the API can help to highlight and prevent potential Business Email Compromise (BEC) attacks. Essentially, this is when a cybercriminal conducts a phishing attack through email to convince users to send money somewhere outside the company. Various forms are used, including false invoices to have funds transmitted to a bank account controlled by a hacker.
It is possible that careful review of the information exposed in the Activities API could help you understand what happened if an attacker manages to secure control over a user’s account. However, a busy Office 365 tenant generates so many audit events daily that administrators are likely to lose sight of important data unless they use analytics to analyze, detect, and highlight anomalies. CAS is an example of a product that uses analytics for this purpose, but there are other good third-party products available that can do much the same.
Be Proactive Rather than Reactive
Before rushing to consider how any newly discovered API can help them understand what happens in a BEC, Office 365 administrators can take some simple steps to proactively improve their defences. Here are seven steps to take to improve the security of your tenant against attack.
Use multi-factor authentication (MFA) for user accounts
Yes, it can be a pain when Outlook or other apps pops up an MFA prompt to reauthenticate access to Office 365, but this is a lot better than having your account penetrated by an attacker.
Make sure that auditing is enabled for all mailboxes
When considering how to improve Office 365 security, I’m more worried that Microsoft continues to allow new mailboxes created by Exchange Online to be disabled for auditing by default than I am about undocumented APIs. Fortunately, it is easy to check for unenabled mailboxes and enable them with PowerShell:
Get-Mailbox -RecipientTypeDetails UserMailbox, SharedMailbox -ResultSize Unlimited -Filter {AuditEnabled -eq $False } | Set-Mailbox -AuditEnabled $True
Microsoft has recently updated the set of auditable events for mailbox auditing to include actions like updating inbox rules, so it might be a good idea to review your configuration.
Update: On July 12, Microsoft announced that they will enable auditing for Exchange mailboxes by default. However, this change will take some time, so be sure to check that your mailboxes are enabled now…
Stop email forwarding outside the organization
Use the forwarding report in the Security and Compliance Center to know if any mailboxes have forwards set outside your domain. Attackers often use inbox rules or set forwards on mailboxes to capture copies of messages to allow them to understand with whom the mailbox owner communicates.
Review failed login attempts
You can do this by searching the Office 365 audit log. Here’s how to do it with a PowerShell search:
$Records = (Search-UnifiedAuditLog -StartDate 15-May-2018 -EndDate 6-Jul-2018 -Operations UserLoginFailed -SessionCommand ReturnLargeSet -ResultSize 5000)
In passing, I note that Office 365 created an extraordinary number of audit records for failed login events in May and June 2018. The problem seems to have gone away now. All of which proves that APIs are sometimes unreliable.
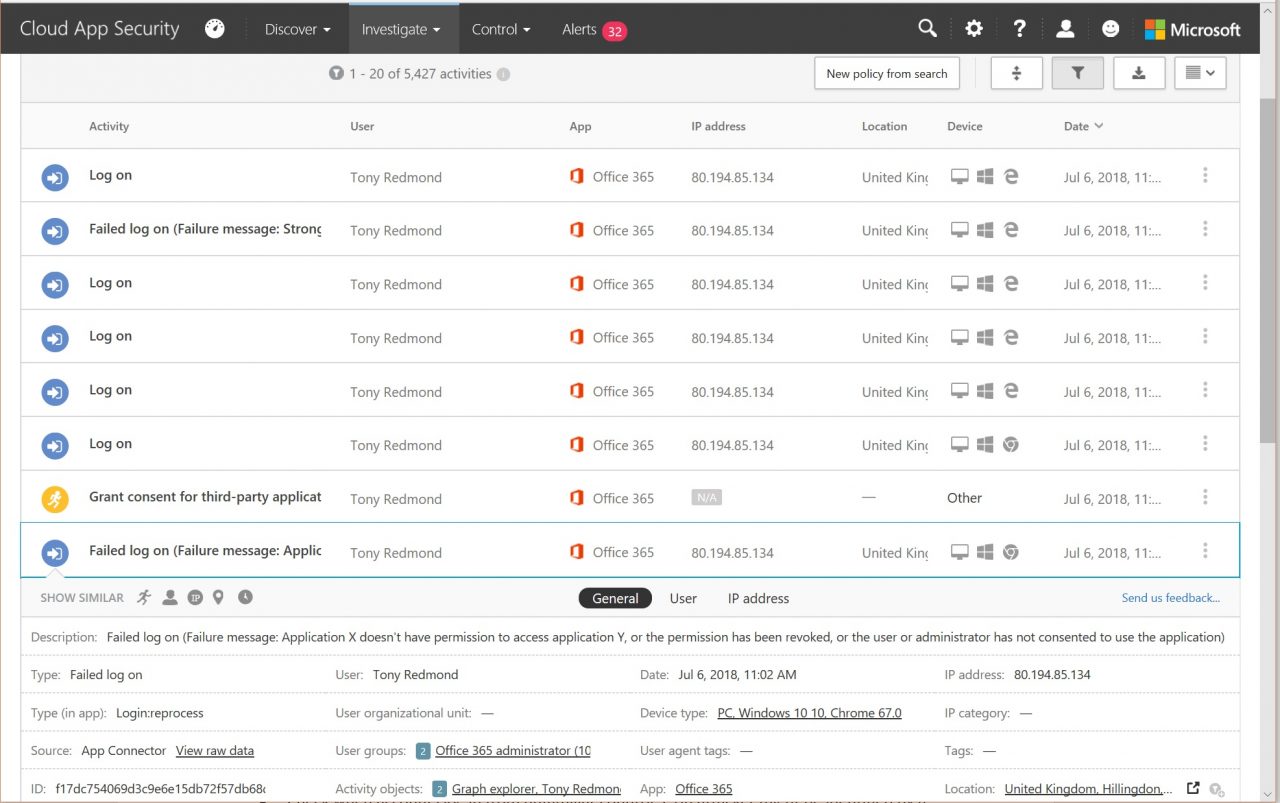
Alternatively, CAS highlights failed login attempts and give some information about the context of the failure (Figure 1).
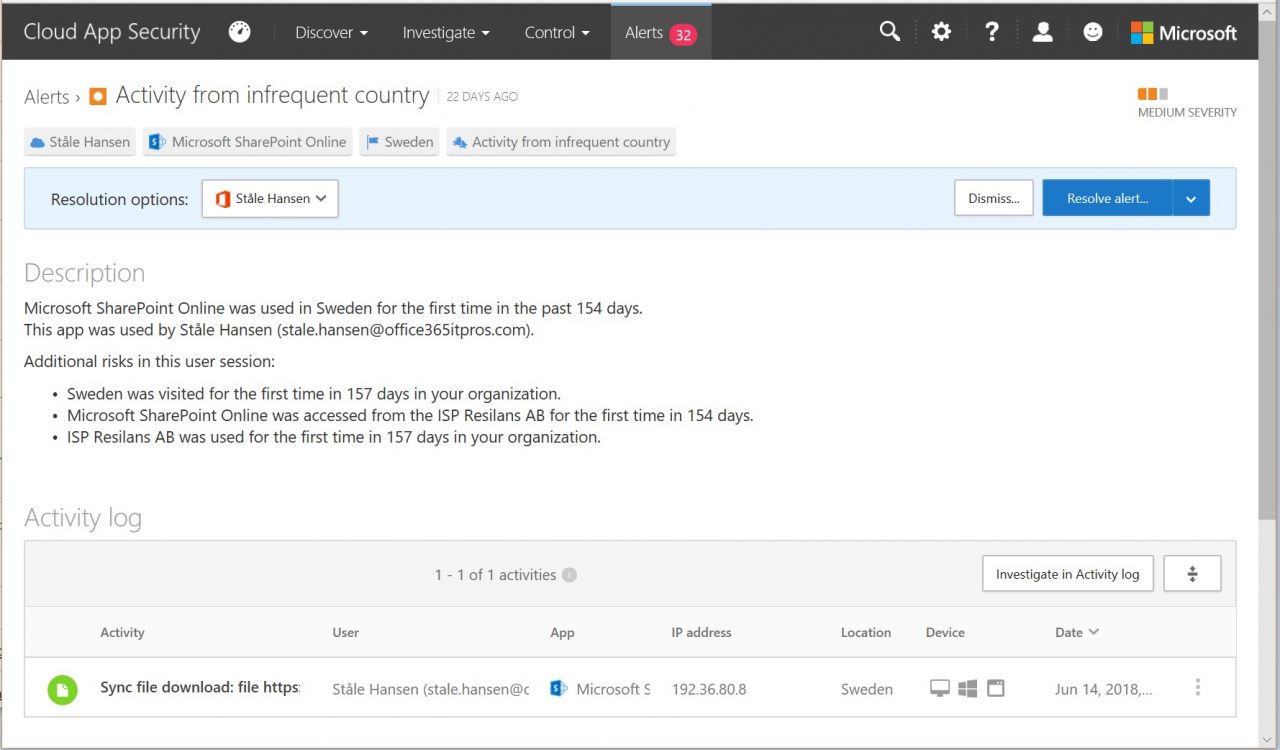
Check when accounts log in from unfamiliar countries
An attacker might be identified by a login from a foreign country (one that the account owner doesn’t usually login from). The Azure AD Portal includes a “Risky Sign In” report or, if you have CAS, you can use it to highlight and resolve unusual activities like the one shown in Figure 2.
Use Activity Alerts or Alert Policies to Report Audit Events
Administrators can create activity alerts or alert policies in the Security and Compliance Center to look for specific events in the Office 365 audit log and warn when these events happen. Although the alerts can only sound after an event occurs, it is still useful to know when something happens.
Use Azure Information Protection to encrypt communications
You can configure templates so that known recipients outside your domain can read protected information, and any Office 365 user can now encrypt messages to any destination. Even better, you can configure a transport rule to encrypt all email sent to selected domains.
Stay Calm and Stay Focused
It’s easy to become excited when a blog reveals some new information that seems important at first glance. Office 365 is a complex suite of applications and its management is complex too (something that Microsoft could improve), but there’s lots of ways to use the data already available to you to resist the kind of attacks contemplated in the recent revelations. Remember, being proactive is always better than being reactive when it comes to security.
Follow Tony on Twitter @12Knocksinna.
Want to know more about how to manage Office 365? Find what you need to know in “Office 365 for IT Pros”, the most comprehensive eBook covering all aspects of Office 365. Available in PDF and EPUB formats (suitable for iBooks) or for Amazon Kindle.




