Potential Problems Lurk When OneDrive Users Block Office 365 Searches
Searching is Critical for Office 365
As you probably know, Office 365 indexes content from multiple workloads to use as the foundation for data governance features like content searches (including GDPR DSRs), eDiscovery cases (including advanced eDiscovery), and Data Loss Prevention policy checking for SharePoint Online and OneDrive for Business. Advanced Data Protection also uses the content indexes to detect malware in newly uploaded documents. In short, it’s important that the content indexes are accurate and kept updated.
But here’s the problem: OneDrive for Business sites are personal. They’re designed to be used by individual users to store personal files. Microsoft has even made it easy to redirect important Windows folders like My Documents to a user’s OneDrive for Business site. SharePoint Online underpins OneDrive for Business and the user who owns a OneDrive for Business site is the site administrator.
Site Owner = Site Administrator
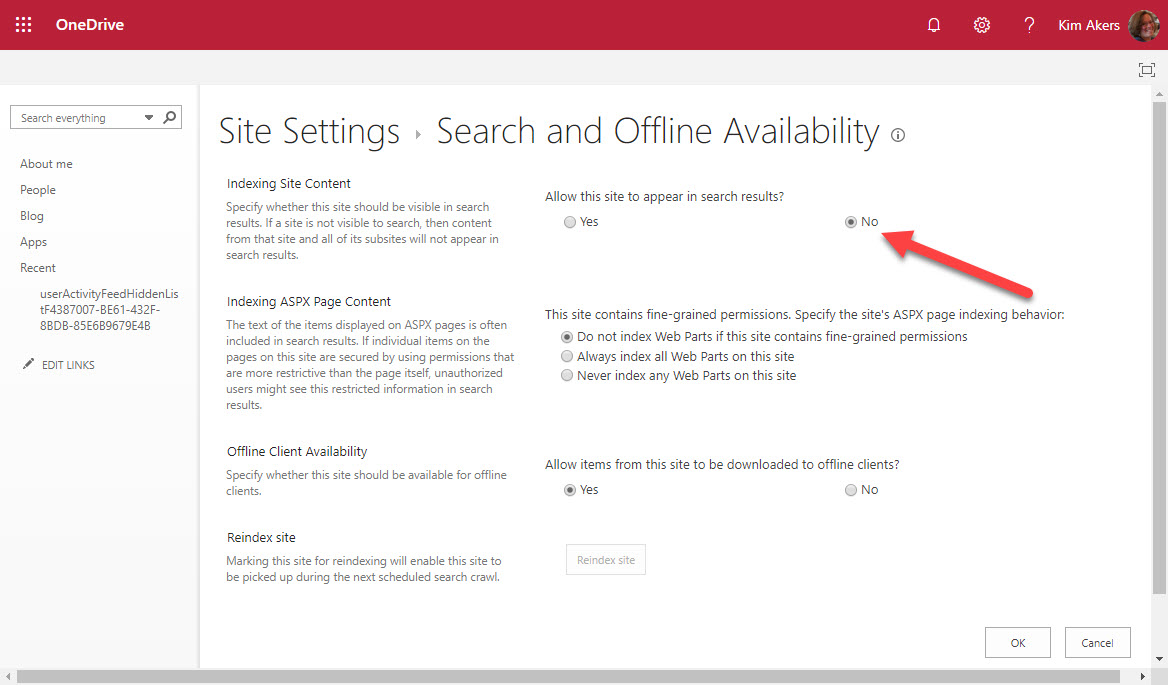
All good so far. What’s not so good is when someone uses their site administrator access to change its site settings to prevent their OneDrive for Business site appearing in search results (Figure 1).
Being able to disable search is a legacy artefact from the earliest implementation of OneDrive for Business based on SharePoint Server 2013 (on-premises). At that time, eDiscovery wasn’t such a big thing, and it was OK for someone to block search from their private files. The equivalent in email terms is when an Exchange user keeps messages in a PST file, which is also invisible to search.
No Content Index, No Features
But when a OneDrive for Business site is excluded, it means that the files in the site won’t be indexed and won’t be available to content searches. It also means that any other Office 365 feature that depends on search indexes won’t work.
Currently, tenant administrators cannot stop users disabling search for their OneDrive for Business sites. In fact, there’s no out-of-the-box mechanism for tenant administrators to even know that a OneDrive for Business site is excluded from search results. There’s nothing in the OneDrive for Business Admin Center; the SharePoint Online Admin Center ignores these sites; and the Get-SPOSite cmdlet doesn’t include a property to show if a site is included in search results. The only indication that it is might be when an eDiscovery investigator notices that search results don’t include files that they expect to find in a site. It’s not a good situation to be in.
What Microsoft Should Do
Given the importance of search indexes to Office 365, it’s not unreasonable to have an org-wide setting that stops users blocking their OneDrive for Business sites from search results. The setting could be in the OneDrive for Business Admin Center or updatable through the Set-SPOTenant PowerShell cmdlet and Microsoft Graph API. I’d also like to see the search status of a site surfaced in a property available settable by PowerShell and the Graph.
And What Microsoft Say They Will Do
To be fair to Microsoft, they reacted with alacrity after this issue was raised. Mark Kashman (from the SharePoint/OneDrive team) replied in the Microsoft Technical Community on September 9 to say that they have “a planned fix soon to roll out” which means that “people will not be able to disable eDiscovery for their own OneDrive.” Although Microsoft didn’t share details of what the fix will be, they did say that it would be an “action for admins.” We await more details as no timescale has been given for when the planned fix will be available.
[Update: October 18 – Microsoft told me today that a fix has been developed and is now shipping. See this post for details..]
Even if they can’t stop eDiscovery for their OneDrive account, users won’t lose any real functionality because if they want to hide their deepest (or darkest) secrets from search, they simply protect the documents with an Office 365 sensitivity label. Search can then index the document metadata but won’t be able to index the protected content.



