Azure Sentinel is Microsoft’s take on a modern cloud-native Security Information and Event Management (SIEM) solution. While Splunk maybe one of the best known SIEM solutions today, Sentinel differs in that it is designed from the get-go to straddle cloud and on-premise infrastructure. Sentinel automatically scales when you need to collect more data and you only pay for what you use. It collects, detects, investigates, and responds to threats. Sentinel can surface suspicious activity and take necessary action to respond to incidents using built-in AI to reduce noise so you can quickly focus on real security incidents.
For more information about Azure Sentinel and how to get started with it, check out Cloud-Native SIEM and Built-in AI for Analytics with Azure Sentinel on Petri.
Configure a Data Connector for Windows Server
Before you can pull data into Sentinel, you’ll need to configure a Log Analytics workspace and add it to Sentinel.
- Open Sentinel in the Azure management portal. If Sentinel is not pinned to the dashboard, type sentinel in the search box at the top of the portal window and then click Azure Sentinel in the list of results.
- Click + Add on the Azure Sentinel workspaces
- On the Choose a workspace to add to Azure Sentinel panel, click Create a new workspace.
- On the Log Analytics workspace panel, make sure that Create new is selected.
- Give the new workspace a name, select the Azure subscription it should be associated with, and select or create a new resource group for the workspace.
- Select a location for the workspace using the Location dropdown menu.
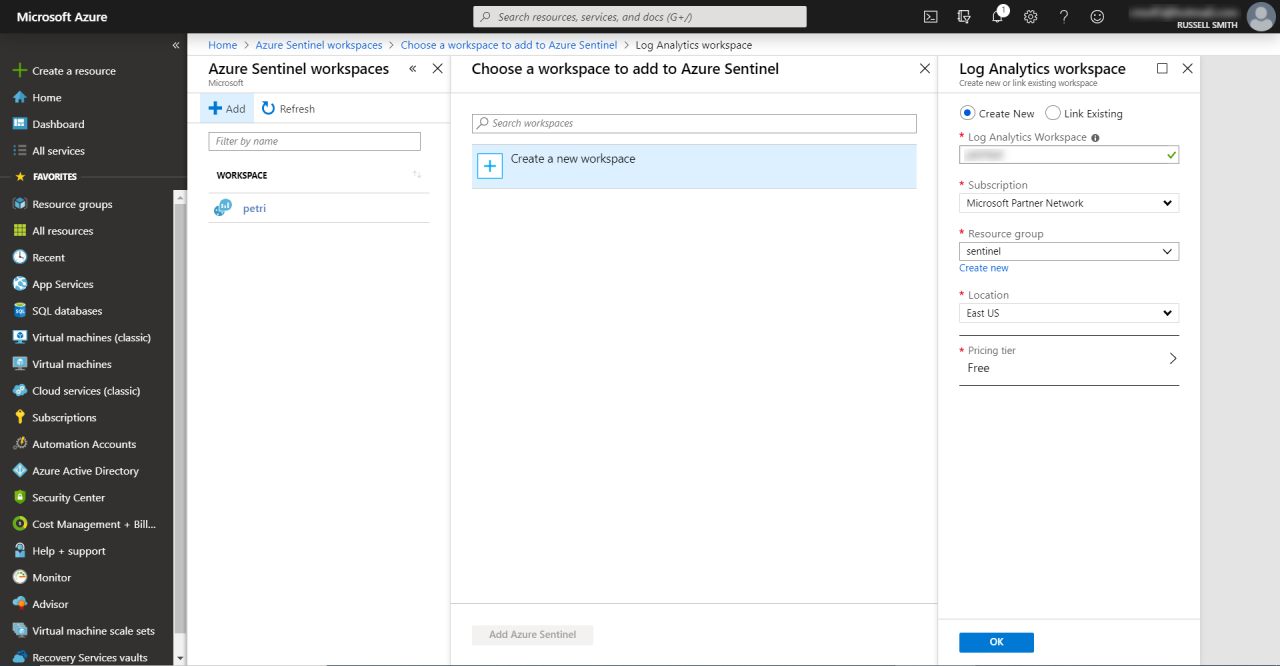
- Finally, select a pricing tier. Note that the Free tier deletes data older than 7 days.
- Click OK in the Log Analytics workspace
- The workspace might take a couple of minutes to deploy.
- Once deployment has completed, select the new workspace in the Choose a workspace to add to Azure Sentinel panel and click Add Azure Sentinel. After a few seconds, you’ll be automatically redirected to the new workspace.
Let’s add a data connector for Windows Server to the workspace. Note that your Windows Server must be able to connect to the Internet. If your server doesn’t have Internet connectivity, you will need to use a proxy to establish a connection to Azure Sentinel but that is out of the scope of this article.
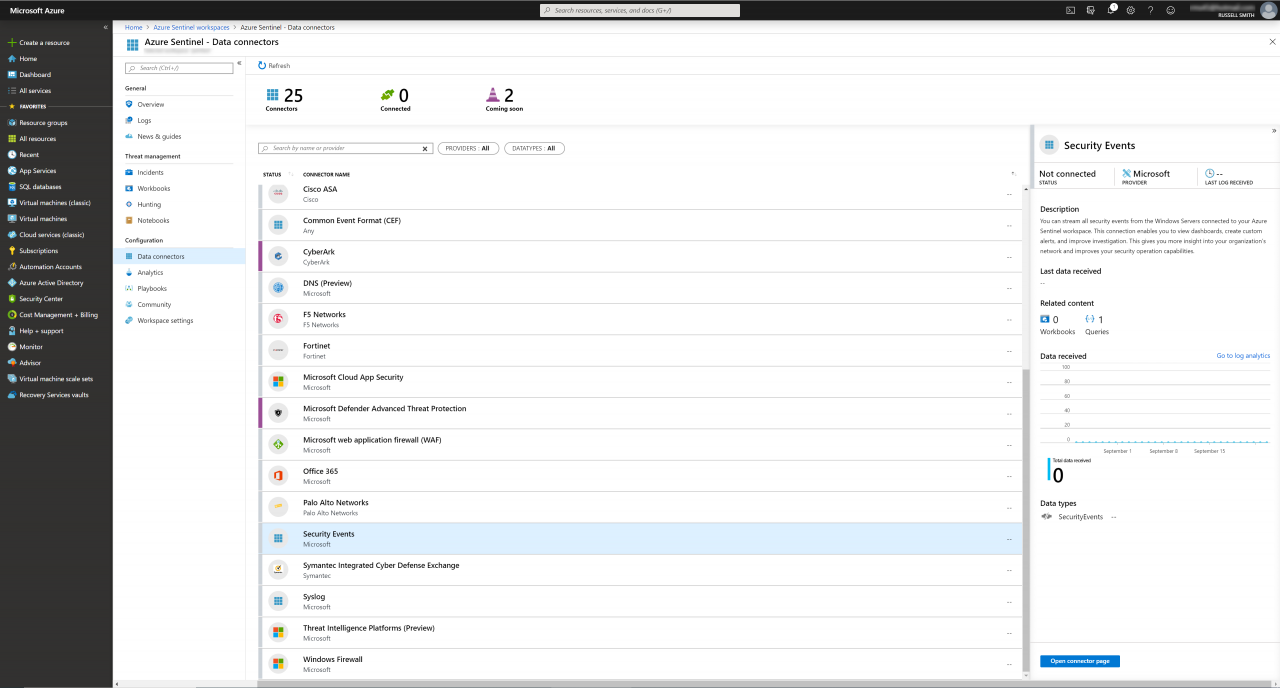
- Click Data connectors under Configuration on the left.
- In the list of data connectors on the right, scroll down and click Security Events.
- In the right bottom corner of the portal, click Open connector page.
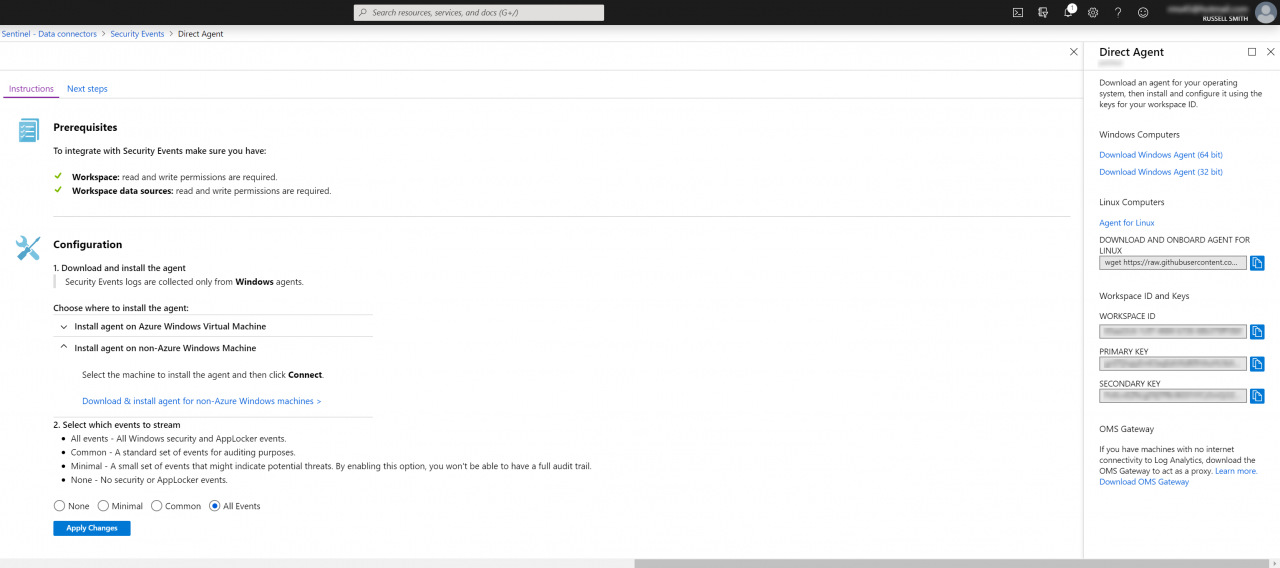
- On the Instructions tab under Configuration, expand Install agent on non-Azure Windows machine.
- Click Download & install agent for non-Azure Windows machines >.
- Download the Windows agent from the Direct Agent panel.
- Run the downloaded executable on the Windows Server from which you want to collect event log data.
- Click Next on the agent welcome screen.
- Click I Agree to accept the terms and conditions.
- Click Next on the Destination Folder screen to accept the default install location.
- On the Agent Setup Options screen, make sure that Connect the agent to Azure Log Analytics (OMS) is checked and then click Next.
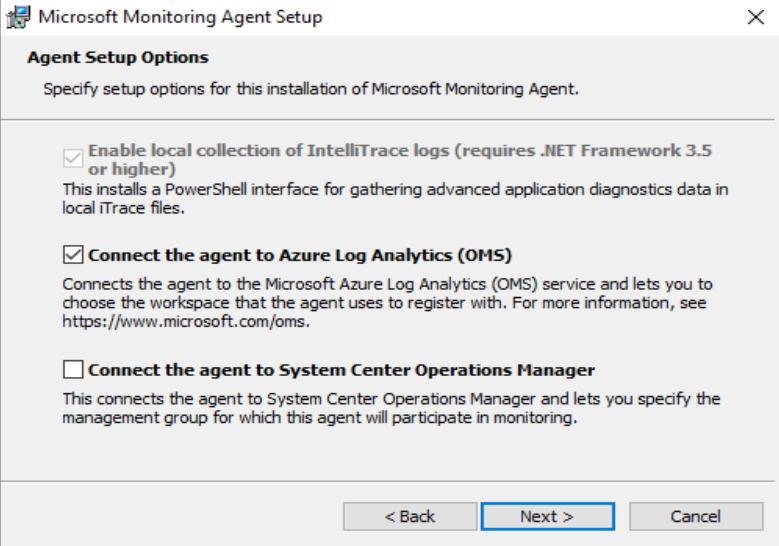
- On the Azure Log Analytics screen, paste your Workspace ID and Workspace Key from the Azure portal.
- Make sure that Azure Cloud is set to Azure Commercial unless you are using US Government or China clouds.
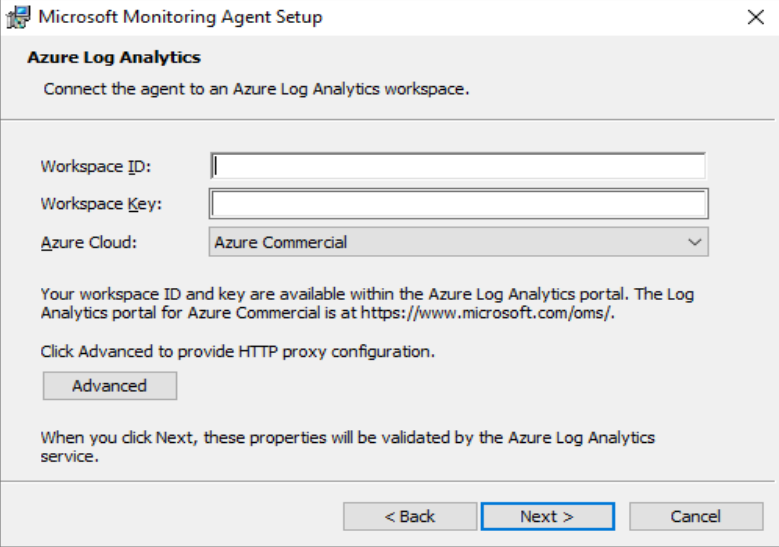
- Click Next to continue.
- On the Microsoft Update screen, select Use Microsoft Update when I check for updates if you want the agent to be updated automatically. Otherwise, leave the default setting and click Next.
- Click Install to complete the process.
- When the install is complete, click Finish.
- Back on the Instructions tab of the Security Events panel in the management portal, select which events to stream. I selected All Events. Click Apply Changes.
That is it. You will have to wait for events to start streaming in. I can take up to an hour. In the second part of this article, I’ll show you how to view and work with the events collected from your Windows Server.




