Unless you have been hiding under an air-gapped rock, the entire computing industry was set on fire this week with the announcement that SolarWinds platform had been compromised. While we are starting to learn little bits of information about the scale and damage of this attack, Microsoft has begun to share what it has learned during the past few days.
Not long after the attack was made public, Microsoft began moving aggressively with nearly every tool in its arsenal to dig up new details and stop potential threats. This isn’t all that surprising, the company has an entire business unit devoted to these tasks that is running 24/7/365 but this attack is unlike anything we have seen in recent memory.
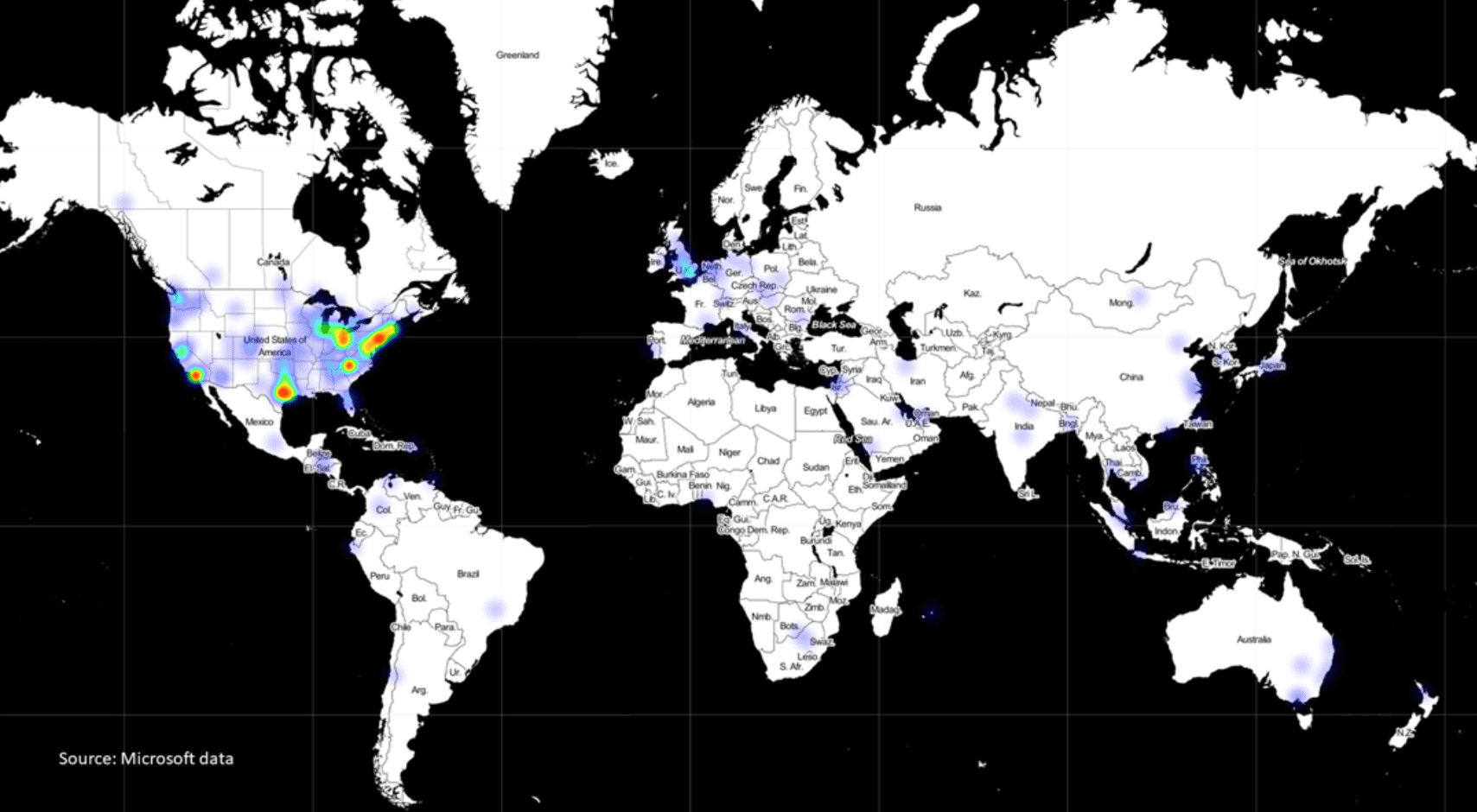
In a post penned by Brad Smith, he highlights some of the facts that SolarWinds already shared including, 17,000 customers being impacted by the breach but also shared new data too. Specifically, that the hackers, stated to be Russian, have targeted 40 organizations of which, 80% are located in the United States.
The targeted list includes not only government agencies, but security and other technology firms. One of the more well-known companies was FireEye who announced that their system and tools had been accessed and stolen. Microsoft was said to be a victim of the attack as well but the company has since denied that allegation.
The full scale and damage of this hack is far from being completely understood. Over the next weeks and months, more information will surface and damage will be announced by companies who were targeted in the attacks.
Security will continue to be an evergreen challenge and as more sophisticated attacks continue to be uncovered, it’s imperative that IT Pros understand how and when to patch their enviornments.