Display Last Interactive Logon Information in Windows Server 2008/2012
Imagine that your network security was compromised and you have a good reason to believe that someone attacked and compromised your domain environment. Or maybe you need to track the number of unsuccessful logon attempts to the domain. Or perhaps the security officer at your organization as asked you for a report. In this article I will show you how to display the last interactive logon information in Windows Server 2008 and Windows Server 2012.
Activate Last Interactive Logon
One of the great features that Windows Server 2008/R2/2012 has to offer is the last interactive logon information. In order to activate last interactive logon, the functional level of the domain must be set at minimum to Windows Server 2008. I will perform these steps and take screenshots on a Windows Server 2008 R2 machine, but it all works the same on Windows Server 2012.
When last interactive logon is activated for the Active Directory domain, the following AD attributes of the user’s object store the relevant information. These attributes are already a part of the AD schema and do not require any modification to AD.
- msDS-FailedInteractiveLogonCount – The number of failed logon attempts since the last interactive logon setting was enabled
- msDS-FailedInteractiveLogonCountAtLastSuccessfulLogon – The total number of failed interactive logons until the last successful logon
- msDS-LastFailedInteractiveLogonTime – The time when the last failed logon attempt occurred
- msDS-LastSuccessfulInteractiveLogonTime – The time of the last successful logon attempt to a workstation
So how do we enable this feature? Let’s start with the basic method, which enables us to save just the information in Active Directory without displaying it to the user. It means that we are going to use a Group Policy Object (or GPO) that applies only to the Domain Controllers that are located under the Domain Controllers’ OU.
- Open Group Policy Management Console (or GPMC) by clicking on Start > Run > and typing gpmc.msc from a Windows Vista/7/2008/R2/8 computer that is a member of the domain.
Note: In order to get the GPMC console on a Windows Vista/7/8 workstation computer, you must have first installed the Remote Server Administrative Tools (or RSAT) on that machine.
Download & Install Remote Server Administration Tools for Windows 7
Download & Install Remote Server Administration Tools for Windows 8
- In the GPMC window, browse to the required GPO that is linked to the OU or domain where the computers are located (in this case we’re using the Default Domain Controllers Policy), then edit it, or, if needed, create a new GPO.
Note: In this case, it is best practice to create a new GPO because later I will use this GPO and link it to another OU.
Create a New GPO:
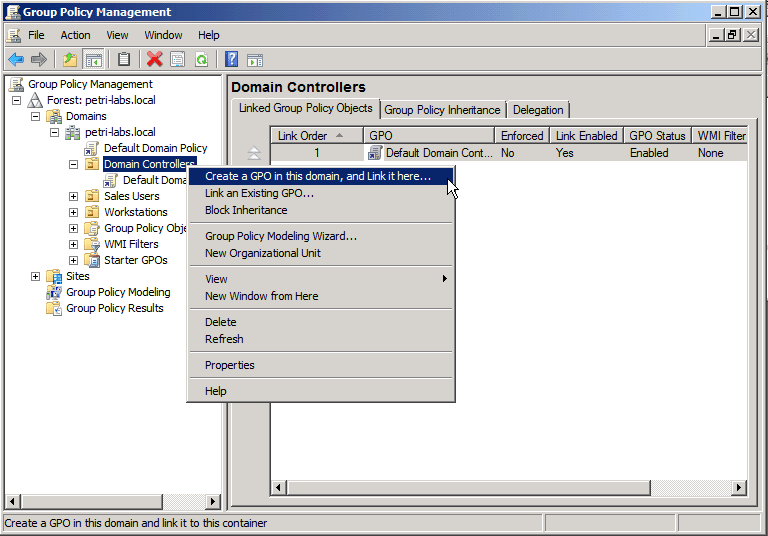
- Select the desired OU, then right click and create new GPO.
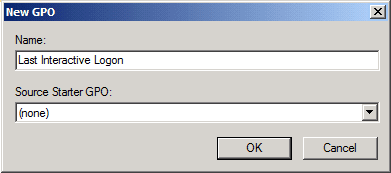
- Give a name to the GPO object.
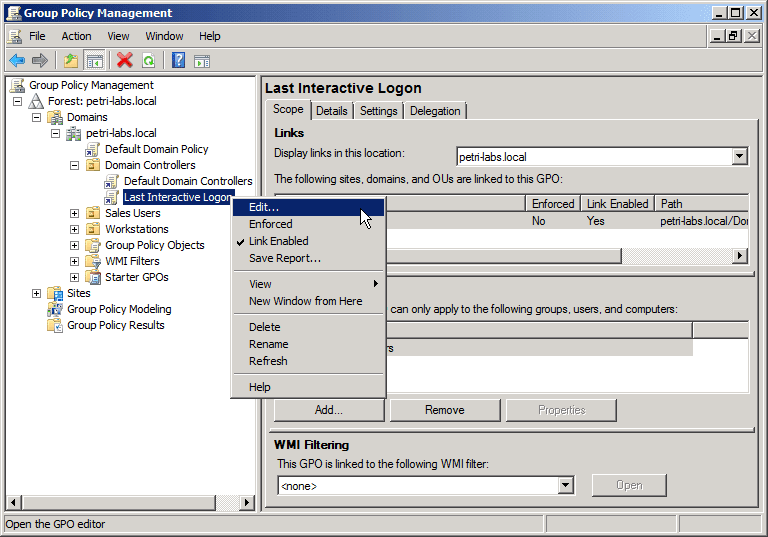
- Select the GPO link that was just created, right-click and select Edit.
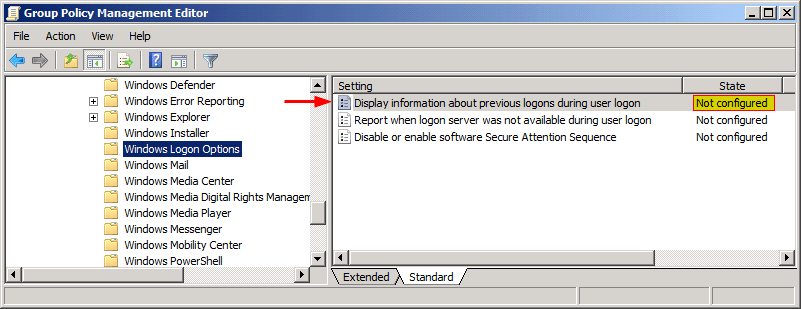
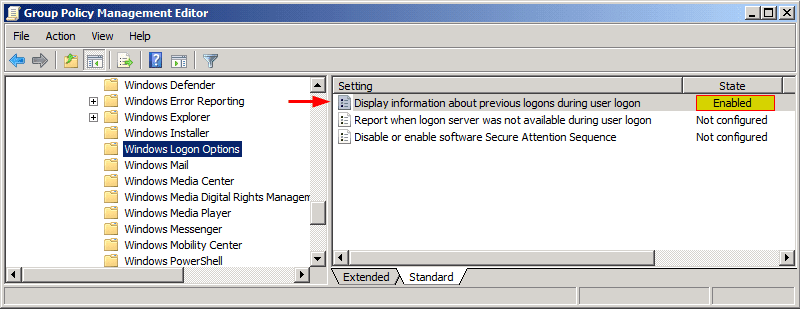
- In the Group Policy Editor window, browse to: Computer Configuration > Policies > Administrative Templates > Windows Components > Windows Logon Options
A setting called “Display information about previous logons during user logon” is not configured by default as shown below.
- Select the setting, double-click, and choose Enabled. Click OK. Your GPO will look like this:
Since we linked the GPO to the Domain Controllers OU, I will restart my demo Domain Controller in order to apply the GPO settings. Of course you can simply use the gpupdate /force command, and you may not need to reboot.
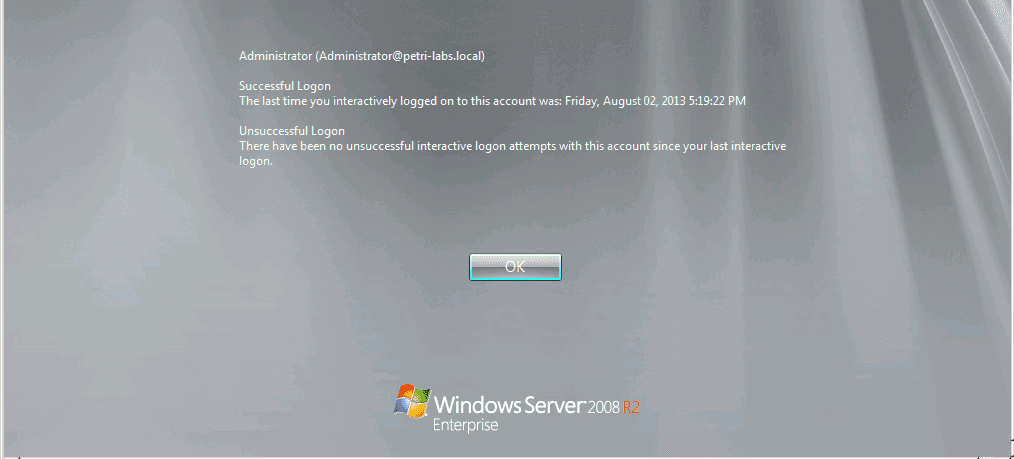
After the machine boots up, when I press Alt+Ctrl+Del to login, after entering the username and password, the following screen is displayed.
We now see logon information regarding the username I used (Administrator) the last time that this user logged on successfully to the domain. I’m informed that since that successful login, there were no unsuccessful attempts for logon.
Display Last Interactive Logon
Now let’s move on, and assume that not only that I want that information to be stored in the Active Directory, but I also want the domain users to see that information when they log on to their workstations.
This will give them the ability to see if someone is trying to use their username and password. For example, say a user knows for sure that the last time she logged on the domain was three days ago. After trying to log on, she sees three unsuccessful attempts to logon and she is absolutely sure it wasn’t her, she knows that someone is trying to guess her password and use her credentials.
Of course, as an administrator you can collect that data using queries that collect the the attributes that I mentioned before, but you can also have users create reports about those events.
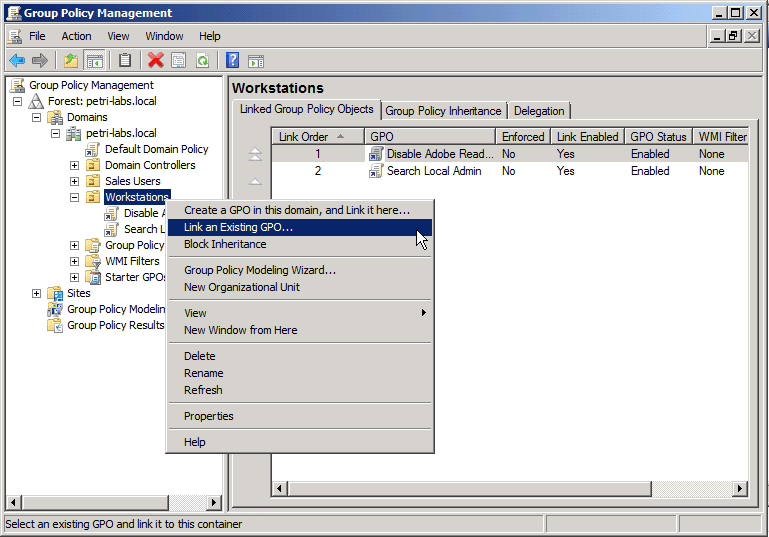
In order to achieve that, we will have to link the GPO we created in our previous steps to the OU where the workstations are located in the AD domain (in this example – the Workstations OU), as shown below.
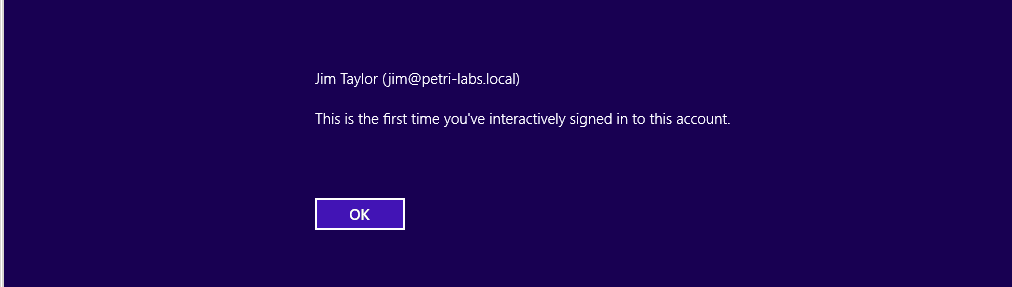
- Choose the “Last Interactive Logon” GPO from the list. I’ve restarted a Windows 8 client computer and logged in as Jim.
You can see that when Jim logs on for the first time after Last Interactive Logon was enabled on the domain, he gets either of these messages: “This is the first time you have interactively logged on to this account” or “This is the first time you’ve interactively signed to this account.”
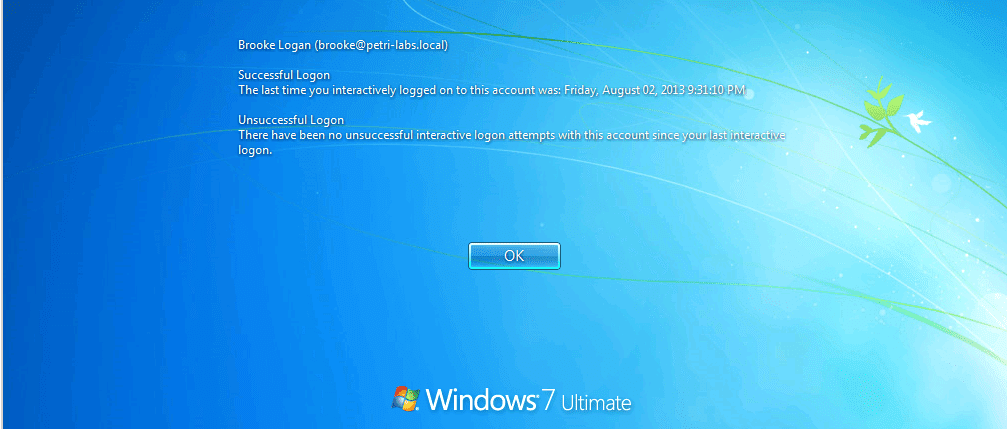
I have restarted a computer called CLIENT1 that is located at the Workstations OU, logged in as Brooke (one of my domain users) and got the following message:
I can see the time and date of the last time Brooke has logged on, and I can also see that since that time, no unsuccessful logons occurred.
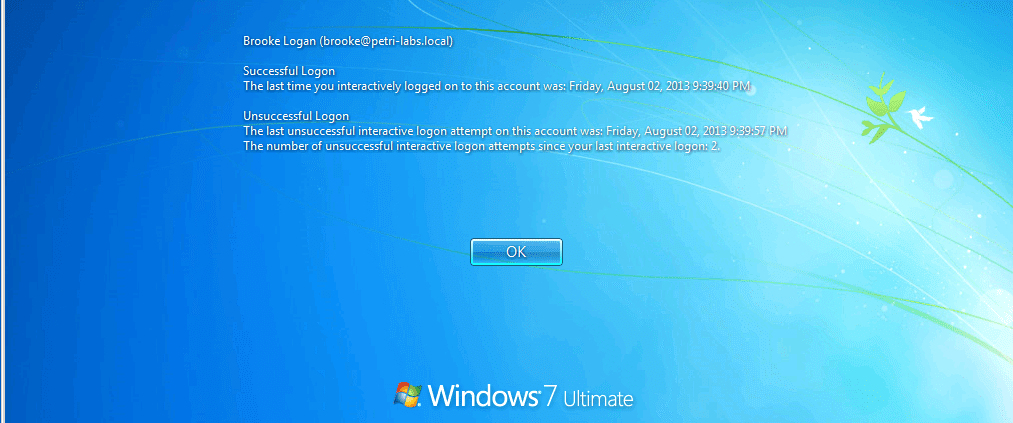
Now, let’s see another example. I logged off from Brooke’s computer (CLIENT1) and tried to log on with her username to another computer, CLIENT2, but this time I deliberately made two mistakes while typing the password. I went back to CLIENT1, typed Brooke’s username and password and this is the message that I got:
I was notified regarding the two unsuccessful login attempts that I made on CLIENT2. Cool!
This interesting feature applies to domain-joined clients running Windows Vista/7/8, Windows Server 2008 /R2/2012.
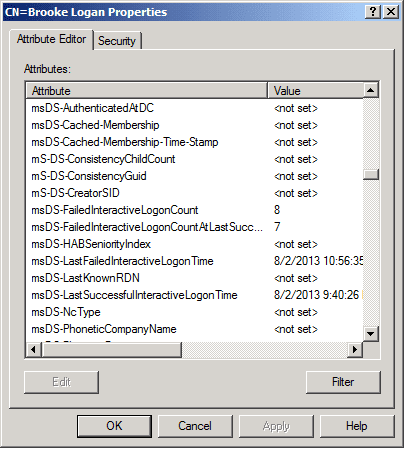
One more thing before we wrap up: If you wondered what it looks like behind the scenes, I used ADSI Edit in order to see the user’s attributes that stored the relevant data.
We can see the time of failed and successful logon as well as the count of failed interactive logons until and from the last successful logon.
Related Article: