I am running a multitude of Windows-based virtual machines hosted on a bunch of virtualization products, ranging from Microsoft Virtual PC and Virtual Server (yes, I need those for most of the Microsoft Official Curriculum courses I teach), Microsoft Hyper-V, along with those hosted on VMware products such as ESX and (my personal favorite) Workstation.
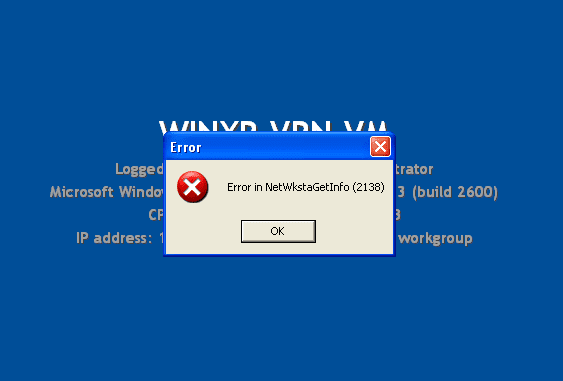
In the past year or so I began receiving strange error when booting up some of my virtual machines:
—————————
Error
—————————
Error in NetWkstaGetInfo (2138)
—————————
OK
—————————
The error came up on some of the virtual machines I used on VMware Workstation, but because after clicking on the “OK” button nothing wrong happened to my machines and I could continue working normally, I never took enough time to investigate the error. This is why I could not pinpoint the exact times when it occurred.
I tried to find a solution for this strange error. I searched Google for the error message but while there were many hits on it, no result seemed to suit my specific environment. Some results did, however, point me to the fact that this error usually appears on VMs running on VMware products.
Another solution I found gave me a hint. It suggested to take a look at the computer’s startup settings by using MSCONFIG, and if that doesn’t help, they suggested repairing the computer’s system files by running SFC SCANNOW. While this command usually repairs the operating system’s system files, I wanted to find something else.
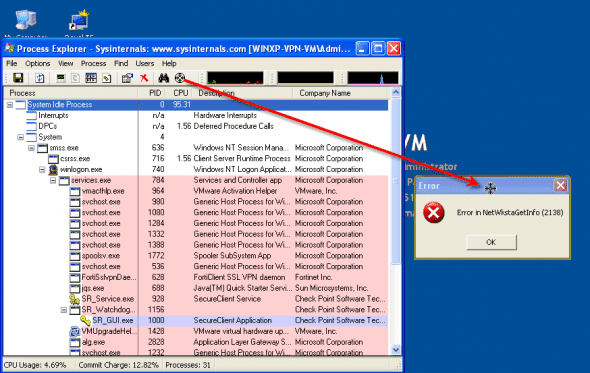
So I moved on, and I wanted to find out exactly what product or software or service or Windows component brought it up. For this I used Microsoft’s (ones – Sysinternals) Process Explorer.
From the product’s site:
Process Explorer shows you information about which handles and DLLs processes have opened or loaded.
The Process Explorer display consists of two sub-windows. The top window always shows a list of the currently active processes, including the names of their owning accounts, whereas the information displayed in the bottom window depends on the mode that Process Explorer is in: if it is in handle mode you’ll see the handles that the process selected in the top window has opened; if Process Explorer is in DLL mode you’ll see the DLLs and memory-mapped files that the process has loaded. Process Explorer also has a powerful search capability that will quickly show you which processes have particular handles opened or DLLs loaded.
The unique capabilities of Process Explorer make it useful for tracking down DLL-version problems or handle leaks, and provide insight into the way Windows and applications work.
Process Explorer:
http://technet.microsoft.com/en-us/sysinternals/bb896653.aspx
So I ran Process Explorer. One of the nice things about it, is the fact that you can use a “target” cross and drag it on top of any visible application (or error message in this case), and be pointed to the executable name and information of the process behind the application or error window.
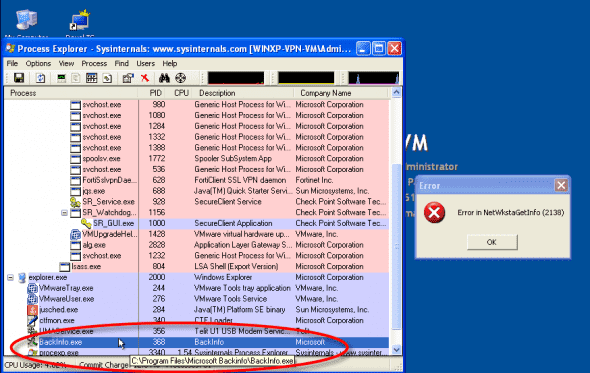
Process Explorer pointed me to the process causing the error. It was in front of my eyes all the time, literally.
Backinfo.exe.
I am using Backinfo.exe to display the netbios name of the machine and information about the CPU, memory,OS, IP address, logged on username and more, and you can clearly see it behind the error message on the first screenshot on this article. Backinfo.exe was once available from Microsoft, but the only working link to download it I found was this:
http://www.impee.co.uk/backinfo/Backinfo.zip
or here:
http://itsupportjournal.com/downloads/backinfo/BACKINFO.exe
Please Note: as the files above are NOT provided/hosted this site, or Microsoft, before running the downloaded file(s) on your system, make sure you properly scan them with decent anti-virus software and use at your own risk!
On the other hand, you can use BGinfo (again, another sysinternals tool):
BgInfo:
http://technet.microsoft.com/en-us/sysinternals/bb897557.aspx
Enjoy.