Windows 7 is the next generation of operating system due from Microsoft and it is still set for a planned release for early 2010 which would be three years after the release of Windows Vista.
This article is an overview of BitLocker and Encrypting File System (EFS) in Windows 7.
[NOTES FROM THE FIELD] – Windows 7 is only in beta release at the time of writing this article and the version that I am using is Windows 7 Ultimate edition, build 6.1.7000.
Because the operating system is in beta release this article should only be considered a preliminary write up and the details are subject to change upon the final release of this new version of Windows.
Encrypting File System (EFS) Overview
When you want to make sure that data access is restricted only to certain individuals you can leverage NTFS permissions to deny access to everyone and to only grant access to those users by way of the access controls provided within the file system. The problem with this is that the security is bound to the file system so as ownership control is gained to the data on a given system at the level of administrator, that file system security is easily undone and access to that data becomes available. When you are the admin with admin level controls to a system you pretty much can do what you want on the system; one of those options is to take ownership of data and change the access control (permissions) of that data.
By leveraging encryption by way of EFS you add on to the NTFS security layer by effectively scrambling the contents of that data so that it can be read only by someone who has the encryption key to decipher it. Just being an administrator of a system is not necessarily going to allow you to gain ownership of the data and the control to access it because now you’d need the key to unlock / decipher the data as well.
There are many forms of encryption in use. Secure Socket Layer (SSL) is leveraged by users on the internet to make secure purchases from retailers or to do online banking. Additionally, when you want to send secured email so that only the intended recipient can open it and read it you would leverage certificate encryption to send that email.
For this discussion we’ll be focusing on security files and folders on a Windows 7 system by leveraging the Encrypting File System (EFS)
[NOTES FROM THE FIELD] – With direct respect to Windows Vista EFS was only available on Business, Enterprise, and Ultimate edition versions.
The various editions of Windows 7 are not fully aligned although some preliminary information is available. I outlined what information that was available in a prior article – Windows 7 Editions Comparison
If Microsoft sticks with the planned editions to be released I would expect that Professional, Enterprise and Ultimate editions for Windows 7 would be the ones that would fully support EFS and the encryption of data.
Windows 7 along with prior supported versions of Windows operating systems allows you to encrypt stored data on the system.
The Process for Encrypting and Decrypting Files
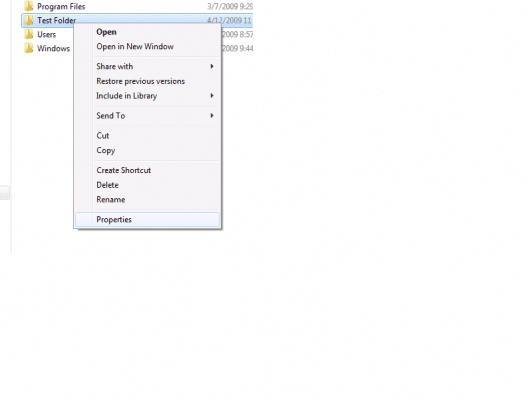
To enable encryption you would right click a folder or file and then choose Properties from the displaying menu.
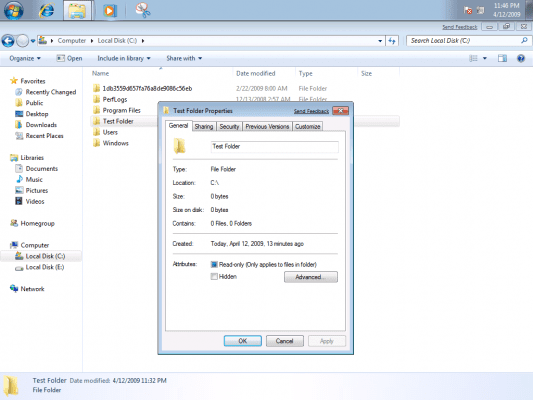
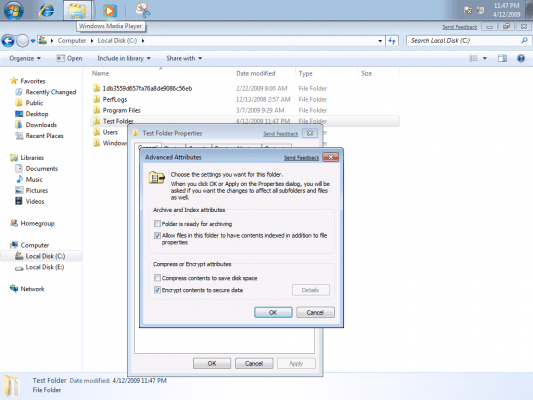
Once the Properties page appears you would click the Advanced button on the General Tab and choose the Select the Encrypt contents to secure data check box, and then click OK.
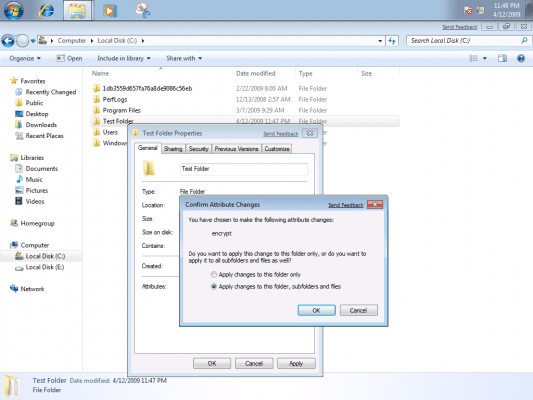
Another dialog box will come up to give you the option of applying the changes to the folder only or to the folder, any subfolders found and the files within.
[NOTES FROM THE FIELD] – It is important to note that once you start encrypting information that you should back up your encryption certificate which is the “key” to lock and unlock the data. If your certificate and key are lost or damaged and you do not have a backup, in most cases where a local system is involved, that encrypted information is lost as it remains forever locked.
There are more recovery options available to you when the system in use is a domain member as there probably is an assigned recovery agent but if you’re using a standalone box you really need to be sure you have the key backed up.
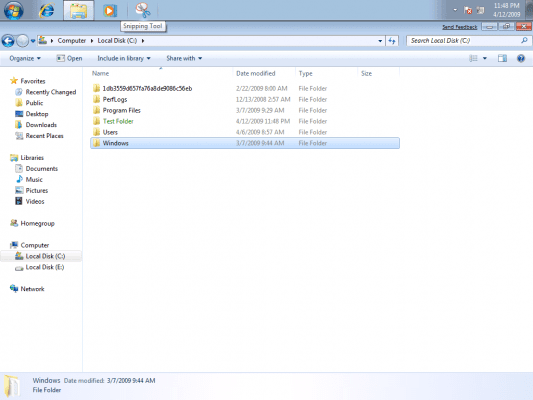
Once the process is complete the data you just selected will be encrypted and you’ll notice this quickly because the folder in Windows Explorer will be green in color.
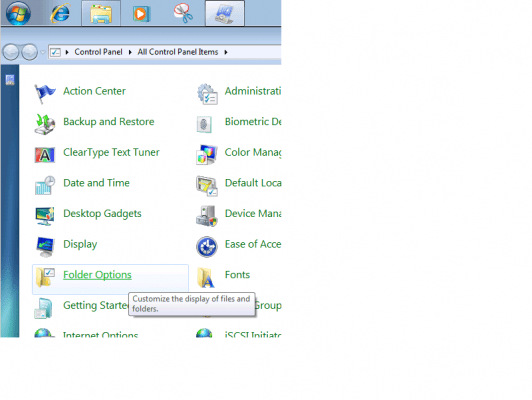
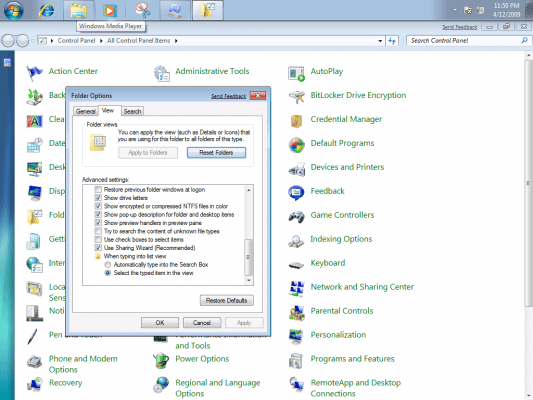
If the data is not show in a different color you can set this in the control panel by selecting Folder Options and choosing the “show encrypted or compressed NTFS files in color”
[NOTES FROM THE FIELD] – Encrypted files will be green and compressed files will be blue.
Encrypted files cannot be compressed via NTFS – in order to compress them you need to use another compression utility (WinZip, compressed folders, etc). If you had some need to only leverage NTFS compression you’d need to decrypt the files first.
Likewise, compressed files (via NTFS) cannot be encrypted without removing the NTFS compression first.
If you want to remove the encryption from a folder or file you simply need to reverse these steps by right clicking the folder or file and then choosing Properties from the displaying menu.
Once the Properties page appears you would click the Advanced button on the General Tab and then clear the Select the Encrypt contents to secure data check box, and then click OK.
Key Thoughts
Some key thoughts with respect to encrypting data by way of EFS:
- On the system where the key is present you are accessing the encrypted data seamlessly by double clicking on it or through another program (e.g. file OPEN process within Word, Excel, etc); there is no other interaction for you. The operating system decrypts the file on the fly to access it and then when it is closed it automatically encrypts it again.
- You need to back up your encryption certificate and encryption key in case you need to recover these if the system crashes or there is some other error and the system needs to be rebuilt and so on. If you neglect to do this and there is an issue and no other recovery agent is available then these encrypted files are forever locked (for all intents and purposes).
- When you encrypt a folder new files or new subfolders that are created in that folder will be encrypted by default. If you need to have a file or subfolder in that folder specifically left unencrypted you’ll need to take that specific action from the properties of that particular object.
- If you copy or move a file to another computer, a different volume or to removable media that does not use the NTFS file system, the file will be decrypted on the copy / move action because the accompanying encryption information cannot be carried over to a file system or device that does not leverage it.
- When there are other users that are going to need access to files or folders that you encrypt they will need to have their own EFS certificate added to the files in order to gain access to them. Think of this like having their own key just to this file. They are not leveraging your key – your key unlocks ALL of your encrypted files; their key when added to a file that you lock with your key allows them to access that data and only that data.
That’s a wrap for my A Security Comparison Overview of BitLocker and Encrypting File System (EFS) in Windows 7 PART 1 – Encrypting File System (EFS) article – I hope you found it a good investment of your time.
In A Security Comparison Overview of BitLocker and Encrypting File System (EFS) in Windows 7 PART 2 – BitLocker I will be reviewing some of the overview details on the Bitlocker functionality as provided within Windows 7.
I am always looking forward to any feedback you have on this or any of the articles I have written so feel free to drop in some comments or contact me directly.
Additionally, I would welcome any suggestions topics of interest that you would like to see and based on demand and column space I’ll do what I can to deliver them to you.
Best of luck in your studies.