Enabling Password-Less Sign-In for Azure Active Directory
Microsoft first enabled password-less sign-in for Microsoft accounts (MSA) using FIDO2 security keys, the Microsoft Authenticator app, and Windows Hello, in the Windows 10 October 2018 Update. Password-less sign-in lets you log in to websites that require a Microsoft account for authentication, like Outlook.com, but using a security key instead of a password.
FIDO2 Password-Less Sign-In for Azure Active Directory
This month, Microsoft expanded password-less sign-in for Azure Active Directory (AAD) to include FIDO2 security keys. Password-less for AAD has been available in public preview since autumn 2018, allowing users to sign in with the Microsoft Authenticator app. Now organizations can start testing password-less sign-in using the same authentication factors available for MSAs, i.e. Windows Hello, FIDO2-based security keys, and the Microsoft Authenticator app.
Windows Hello, the Microsoft Authenticator app, and FIDO2 security keys securely store a private key that can be unlocked using biometric recognition or a PIN. The private key is used to verify the user and device.
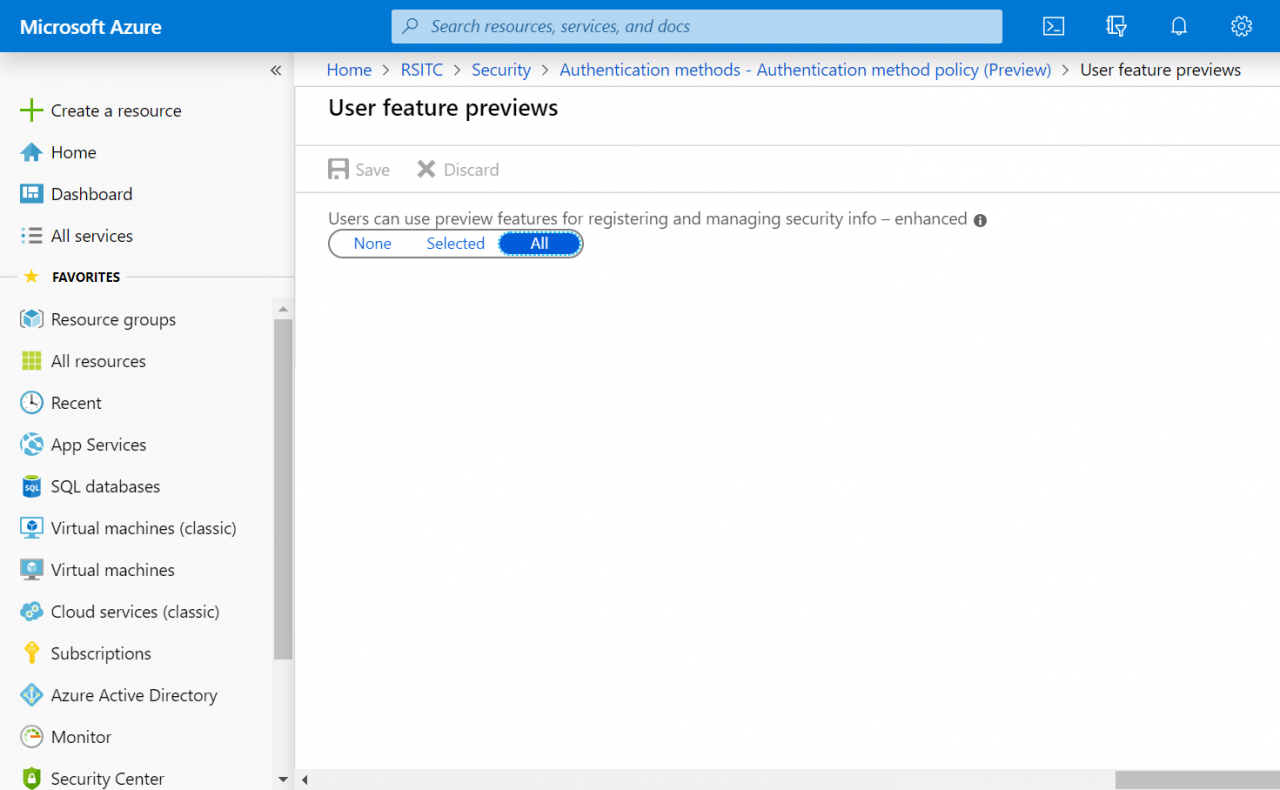
There are also some new admin features in the Azure AD portal for managing authentication factors for users and groups. Microsoft says that you can use these features to manage a staged rollout of password-less authentication. The aim is to create one tool where administrators can manage all authentication factors, including multifactor (MFA), OATH tokens, and phone number sign-in.
Passwords No Longer Effective
Microsoft is pushing password-less sign-in because it believes that passwords are no longer effective. Passwords are inherently weak for several reasons. Users often choose passwords that are easy to guess, can be hacked in a dictionary attack; and people set the same password across different services, making it simple for hackers to compromise multiple accounts. Passwords are also easy to obtain via social engineering, like phishing emails, or using malware that installs a keylogger. Passwords are especially vulnerable when used on devices that might not be secured to the standards of your own PC.
Data shows that 81 percent of successful attacks originate from a compromised password. While multifactor authentication effectively protects passwords by requiring users to verify their identity with a security challenge, like accepting a log-in request using an authenticator app or confirming a code sent to the user’s registered mobile number, MFA has a low adoption rate and isn’t necessarily easy to set up and manage.
Enable Password-Less Sign-In for Azure Active Directory
You can enable password-less sign-in for Azure AD in the new Authentication methods blade in the Azure AD management portal. Password-less sign-in can be enabled for all users or select groups.
Once password-less sign-in is enabled, users can manage their sign-in methods at https://myprofile.microsoft.com/ by clicking Security info. To add a FIDO2 security key, users will need to have already set up at least one Azure MFA method.
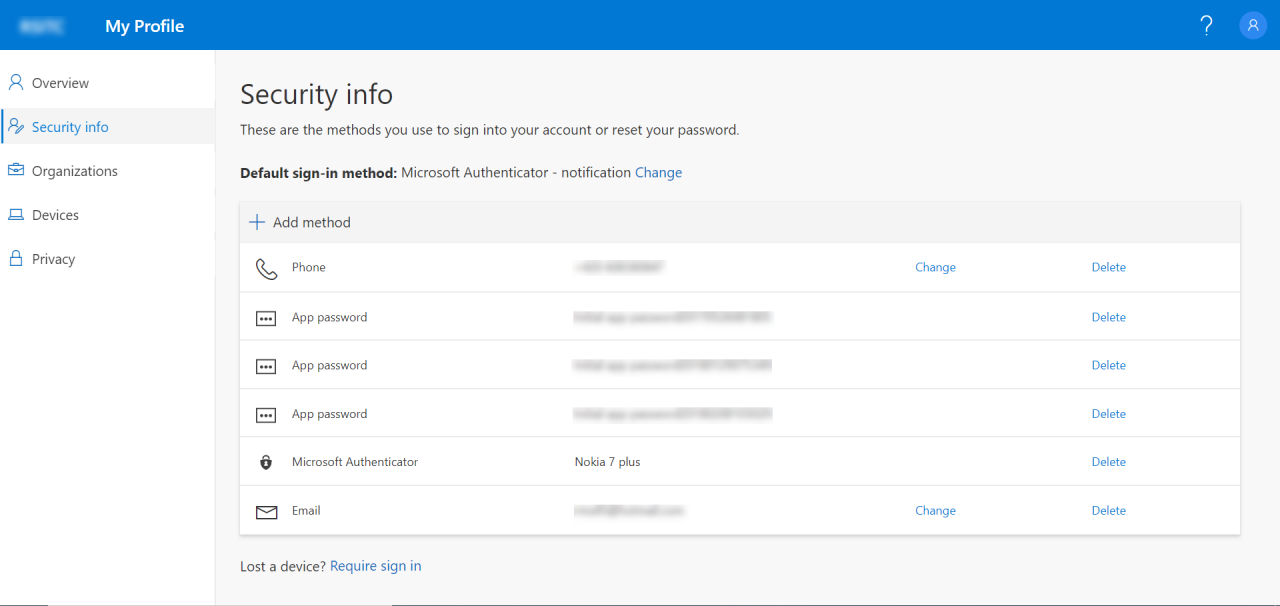
Once a security key has been added, it can be used to sign in to Windows 10 and sign in to websites when using the latest versions of Edge (Windows 10 1809 or later) and Firefox.
Security keys are more likely to be deployed by large organizations. But the more convenient and secure sign-in options Microsoft provides, the more likely companies and users will adopt password-less sign-in. We’re a long way off from seeing password-less sign-in become the norm, and with all the legacy browsers and versions of Windows out there that don’t support this technology, it’s going to be a long and slow journey. But as Microsoft rightly points out, we can’t rely on passwords for a secure future.




