Dynamic Access Control: Configure and Deploy Central Access Policy, Configure File Server
Welcome back to our series on Dynamic Access Control (DAC)! In part one I gave you an introduction to Dynamic Access Control (DAC) in Windows Server 2012, and in part two, I looked at how to enable Kerberos support for claims and how to define claim types and resource properties. Now, in part three of this series, I’ll describe how to configure central access rules and policies, how to distribute them using Group Policy, and how to apply a central access policy to a folder.
DAC: Configure a Central Access Rule
Central access rules determine the conditions that should be met before access is given to a resource. We’ll take the claims and resource properties that we defined in part two of this series and require that a user’s Department and Country claims match the file Department and Country resource properties.
- Log on to your Windows Server 2012 domain controller as a domain administrator.
- Open Server Manager from the desktop Taskbar or from the Start screen.
- Select Active Directory Administrative Center (ADAC) from the Tools menu in Server Manager.
- In the left pane of ADAC, click Dynamic Access Control.
- In the central pane, click Central Access Rules.
- In the Tasks pane on the far right of ADAC, click New > Central Access Rule.
- In the Create Central Access Rule window, type Dept_country_match in the Name box.
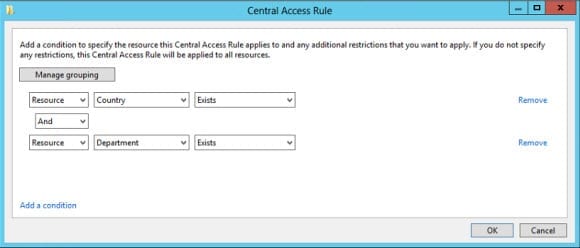
In the first part of this rule, we’ll set a condition that the Country and Department resource properties must exist on the file to be evaluated.
- Under Target Resources, click Edit. In the new Central Access Rule dialog, click Add a condition.
- Now you’ll see a series of drop-down menus appear in the dialog to allow you to create a condition. In the third drop-down menu from the left, change Equals to Exists. Leave the first menu set to Resource and make sure the second is set to Country.
- Click Add a condition again. In the third drop-down menu from the left, change Equals to Exists. Leave the first menu set to Resource and the change the second to Department.
- Click OK.
Now let’s create a conditional expression to secure a resource. While in this walkthrough we are using central access policies to distribute rules to file servers, the steps below could equally be performed in the advanced security settings editor of the security descriptor.
- Under Permissions in the Create Central Access Rule window, make sure that Use following permissions as current permissions is checked.
The default Use following permissions as proposed permissions setting only creates audit log entries and is useful for testing the impact of DAC rules.
- Now click Edit under Permissions.
- Click Add in the Advanced Security Settings for Permissions dialog.
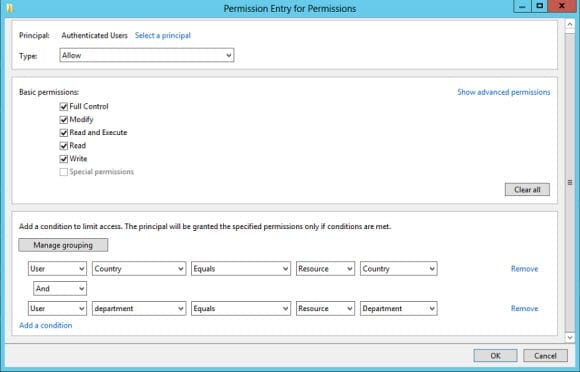
- In the Permission Entry for Permissions dialog, click Select a principal.
- In the Select User, Computer, Service Account, or Group dialog, type Authenticated Users in the Enter the object name to select box and click OK.
- Back in the Permission Entry for Permissions dialog, check Full Control under Basic permissions.
- Now click Add a condition. A series of drop-down menus will appear.
- In the first column, select User. Continue from left to right selecting: Department, Equals, Resource, and finally Department.
- Click Add a condition again. This time, select in the drop-down menus from left to right: User, c, Equals, Resource, Country.
- Click OK in the Permission Entry for Permissions dialog.
- Click OK in the Advanced Security Settings for Permissions dialog.
- Click OK in the Create Central Access Rule window.
Add Central Access Rule to Central Access Policy
Before we can distribute the rule to a file server, we need to add it a central access policy.
- In the left pane of ADAC, click Dynamic Access Control.
- In the central pane, click Central Access Policies.
- In the Tasks pane on the far right of ADAC, click New > Central Access Policy.
- In the Create Central Access Policy window, type Dept_country_match in the Name box.
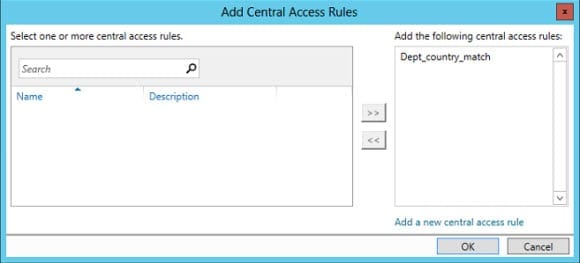
- Click Add under Member Central Access Rules.
- In the Add Central Access Rules dialog, select Dept_country_match in the left column and click the >> in the center to add the rule to the right column. Click OK.
- Now click OK in the Create Central Access Policy window.
Publish the Central Access Policy Using Group Policy
Now let’s create a new Group Policy Object (GPO) to publish the policy to our file servers.
- Open the Group Policy Management Console (GPMC) from the Start menu or the from the Tools menu in Server Manager.
- In the left pane of GPMC, expand your AD forest and domain.
- Right-click the Group Policy Objects folder and select New from the menu.
- In the New GPO dialog, name the GPO Dynamic Access Control and click OK.
- Click the Group Policy Objects folder in the left pane.
- Right-click the new GPO in the right pane of GPMC and select Edit from the menu.
- In the Group Policy Management Editor window, expand Computer Configuration > Policies > Windows Settings > Security Settings > File System.
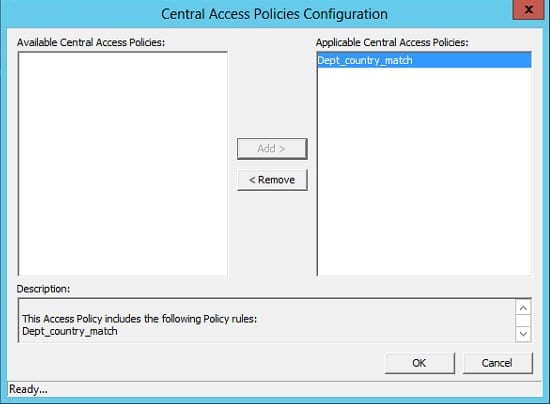
- Right-click Central Access Policy under File System and select Manage Central Access Policies from the menu.
- In the Central Access Policies Configuration dialog, select Dept_country_match in the left column and click Add. Now click OK.
- Close the Group Policy Management Editor window.
- In the left pane of GPMC, right-click your AD domain or an Organizational Unit (OU), and select Link an Existing GPO here from the menu. In this example I have an OU that contains all my file servers and will link the GPO here.
- In the Select GPO dialog, choose the Dynamic Access Control GPO and click OK.
Configure a Windows Server 2012 File Server to work with Dynamic Access Control
Now that Group Policy has updated and DAC policies are available to my file servers, let’s configure a shared folder on one of the file servers with classification properties. On a Windows Server 2012 file server with the File Server Resource Manager (FSRM) feature installed, log on with an account that has local administrator permissions:
- Open File Explorer using the icon on the desktop Taskbar.
- Navigate to a shared folder in File Explorer.
- Right-click the folder and select Properties from the menu.
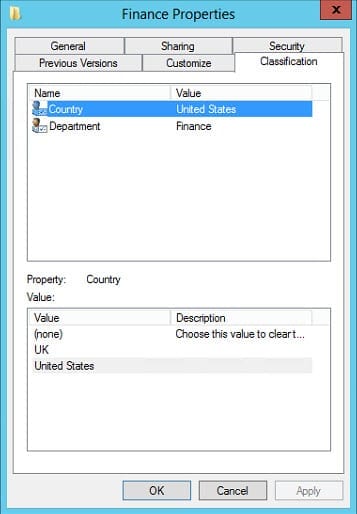
- In the folder’s Properties dialog, switch to the Classification tab.
If you don’t see the Country and Department resource properties in the Classification tab, you can run the following PowerShell cmdlet to force an update on the local file server: Update-FSRMClassificationPropertyDefinition
- Click the Country resource property in the top part of the dialog, and then select United States from the list of suggested values at the bottom. Do the same for the Department resource property but select Finance for the value. Now click Apply.
- Switch to the Security tab in the folder’s Properties dialog.
- Click Advanced at the bottom of the Security tab.
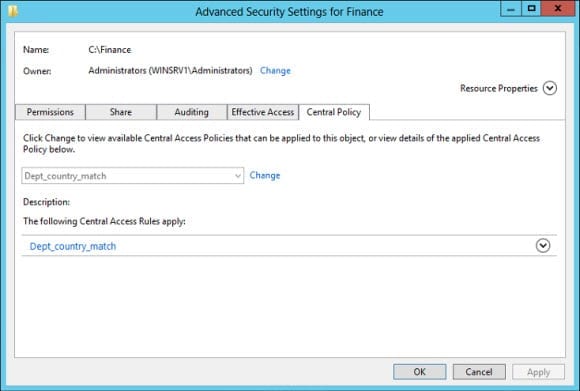
- In the Advanced Security Settings dialog for the folder, switch to the Central Policy tab. Note that you won’t see this tab unless the Dynamic Access Control Group Policy Object has applied to the file server.
- Click Change and select Dept_country_match from the drop-down menu. Now click OK.
Effective Permissions for Conditional Expressions
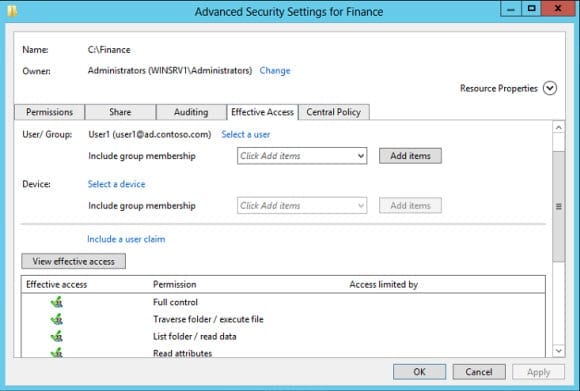
Before users can access files, any existing NTFS permissions must allow that access. If a conditional expression exists, the result of all expressions must be true for a given user or device before access is granted. Conditional expressions are processed after and in addition to NTFS permissions. They can only apply to files and folder, not share permissions.
In this example I have a folder called Finance on one of my file servers where Authenticated Users have Full Access at the share and file system level. I’m now going to check for effective permissions to see if users in Active Directory with Country and Department attributes set to United States and Finance respectively can access the folder. Additionally, I’ll also check that users who don’t have one or both of the attributes set to meet the conditions in the rule are denied access.
- Switch to the Effective Access tab in the Advanced Security Settings dialog.
- Click Select a user to the right of User/Group.
- In the Select User, Computer, Service Account, or Group dialog, type the name of a user that has Country and Department attributes in AD set to United States and Finance respectively in the Enter the object name to select box. Click OK.
- In the Advanced Security Settings dialog, click View effective access.
Unless there are any NTFS file permissions specifically denying the user access, you should see that the user has access to all the permissions listed. Repeat the above procedure to view effective access for a user that doesn’t have either the Country or Department attribute in AD set to United States or Finance, and you should see that access is blocked, regardless of the NTFS permissions set on the folder.