In part 1 in this article series, I discussed plans on how to build a production-ready standalone Windows Server 2012 R2 Hyper-V host. In that article, we learned how to install the management OS, update drivers and firmware, and create a NIC team. In part 2, I showed you how to enable Hyper-V and configure the host networking. In this final article for this series, I’ll show you how to finalize the host and prepare it for production workloads.
Updating the Hyper-V Host
Did you remember to download and install the latest drivers and firmware for your physical computer from the manufacturer’s website? If you are refusing to do this step, then do your client a favor by stepping away from the computer, opening a job hunting site, and begin searching for new job opportunities. If you forgot to do this update, then do it now before proceeding!
Run Windows Update and reboot until there are no remaining updates to install. You’ll need to configure the following:
- Computer Name: Edit the system settings to give the management OS a computer name. This is your host’s identity on the network.
- Domain: Join the management OS to a domain to make management much easier.
- Remote administration: Enable Remote Desktop access so you can log into the management host from your PC.
And then I do what most fail to do by installing the recommended updates for Hyper-V. These updates are not included in Windows Update but they do fix bugs in Hyper-V and related technologies. Browse the list and find the suitable updates. For example, you wouldn’t download an update that applies to hosts with Intel processors if your host has an AMD processor.
Those who are lazy will complain that they have to apply to download and then download each hotfix. Do it once, save them to an administration folder and reuse the hotfix installers in the future. It’s not a big job, and it’s one that is easily delegated to a junior member of staff.
Hyper-V Antivirus Software
I’ll be clear when I say that I detest installing antivirus on Hyper-V hosts because it can be destructive. Instead, I much rather do the following to meet security requirements:
- Restrict administrative access: Not everyone should be a Hyper-V administrator, just like not everyone should be a domain administrator.
- Windows Firewall: Bring the Windows Firewall up to protect the hosts. Maybe you manage this via Group Policy. And no, the Windows Firewall on the management OS has nothing to do with virtual machine networking. The management OS is a completely different computer to the virtual machines, and each has their own security boundary and network presence.
- Internet access: If you’re the sort of person that browses the web and checks email from your servers, then please see my previous career change tip. Although you might need the core network for Hyper-V Replica, I recommend using the core network to block Internet access for the hosts. Maybe you could configure the firewall to control Internet access for the hosts to stop misbehaving administrators.
If you really must install antivirus on your management OS, then follow Microsoft’s security guidelines for Hyper-V hosts with no exceptions, despite what your security (or insecurity?) expert might say. And I was deadly serious about the agreement signed in blood in my previous article!
Install Hyper-V Console on Your PC
If you run Windows Server X, then you must use the Windows X client version or a later version to manage it. If you run Windows Server Y, then you must use the client version of Windows Y to manage it. If you run Windows Server 2012 R2, then you must use Windows 8.1 to manage it.
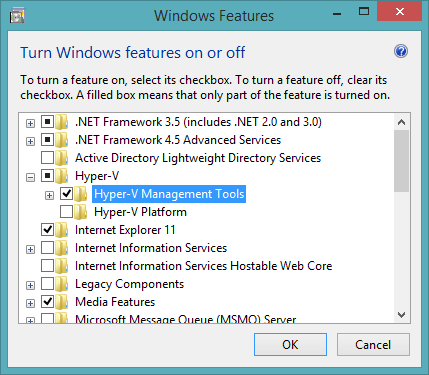
You don’t need to log into a host to manage Hyper-V. You can use System Center, remote PowerShell, or the Hyper-V Manager console on your Windows 8.1 Pro or Enterprise PC. You can get the Hyper-V Manager console by doing the following:
- Open Control Panel
- Launch Program And Features
- Click Turn Windows Features On or Off
- Expand Hyper-V and check the box for Hyper-V Management Tools
Installing Hyper-V Manager on Windows 8.1 (Image: Aidan Finn)
Assuming that you are logged in as a host administrator on a PC that is joined to a domain that trusts the host’s domain, then you can remotely manage Hyper-V from your PC in a couple of minutes.
Enhanced Session Mode in Windows Server 2012 R2
Normally we should try to use Remote Desktop to log into virtual machines for our local administration needs. But there are times when we do need a KVM-style experience that uses a local console, such as:
- Installing the guest OS
- Troubleshooting crashes
- Resolving network issues
- Repairing remote desktop connectivity
The original Connect experience until Windows Server 2012 was a bit basic. We had a very crude way to copy text into a virtual machine, but there was no true copy or paste functionality. Copying files into a virtual machine was a challenge. The performance of the GUI was okay, but not great, as there was no audio. In Windows Server 2012 R2, we were given an improved virtual machine Connect experience, which is known as Enhanced Session Mode.
Enhanced Session Mode gives you a normal copy and paste experience through a RemoteFX (what used to be called RDP) tunnel. You don’t need network connectivity to the virtual machine, but you can get the following advantages and capabilities when connected to a Windows virtual machine:
- Smooth graphics
- Audio redirection
- USB redirection
- Easy file transfer to and from the virtual machine
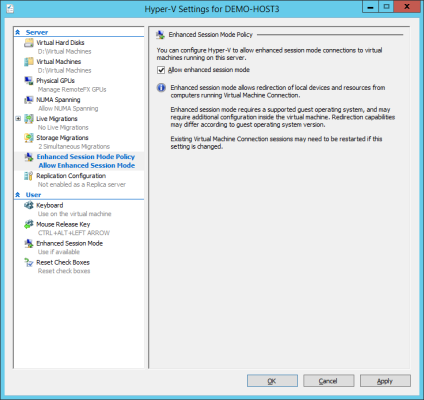
Note that Microsoft disabled this feature by default in Windows Server 2012 R2, which is enabled by default in the Windows 8.1 Hyper-V client. Microsoft’s reasoning was for security reasons, where Hyper-V administrators remain in control over enabling anyone having the ability to transfer files in and out of a virtual machine, which might be seen as an undesirable action in some environments.
You can enable Enhanced Session Mode by editing the host settings in Hyper-V Manager. Browse to Enhanced Session Mode Policy and check the box labelled as Allow Enhanced Session Mode. Subsequent connections to compatible virtual machines will then offer this superior connection experience.
Enabling Enhanced Session Mode on Windows Server 2012 R2 Hyper-V (Image: Aidan Finn)
Live Migration for Your Hyper-V Role
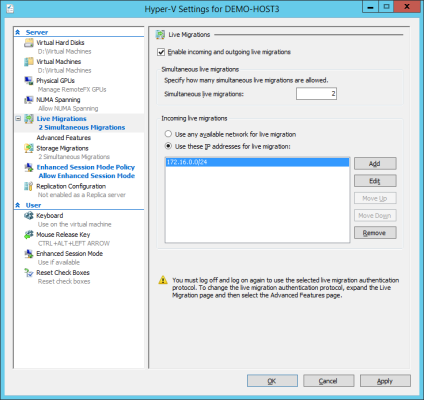
We did not configure Live Migration when we enabled the Hyper-V role. We’ll do it now because we have full visibility of all of the possible options. Once again, edit the settings of the host and browse to Live Migrations.
Check the box to enable Live Migration. You need to ensure that this host has a common network for Live Migration with other hosts (Shared-Nothing Live Migration). You can use any network that the host has access to, or you can choose the option to enter a network IP address. This host has a single network, the management OS virtual network, so we can check the Use Any Available Network For Live Migration option.
Some might choose to enhance their network design by adding a dedicated management OS virtual network for Live Migration and reconfiguring the weight-based Quality of Service (QoS) to protect virtual machine and management OS networking from being crowded out by Live Migration traffic.
Configuring Live Migration in Windows Server 2012 R2 Hyper-V (Image: Aidan Finn)
In the Advanced Features of Live Migrations, you will see some authentication options. I’m not going to discuss that topic in detail here, but CredSSP is the easy one and lets you log into a host and push virtual machines to other hosts. Kerberos provides more flexible administration but requires more setup work.
Upgrade Integration Components in Existing Virtual Machines
At this point you’ve been testing the host with some virtual machines. You might have some older virtual machines that you’re going to live migrate or import onto the new non-clustered Windows Server 2012 R2 host. The last step in the process is to make sure that those older virtual machines are updated with the newest version of the Hyper-V integration components as soon as possible to ensure stability, feature availability, and performance.