Delegate Permission to Reset AD User Account Passwords
How do I delegate permissions to reset user account passwords in Active Directory?
It’s all too often that organizations grant IT staff domain admin rights to Active Directory to perform administrative tasks that require just a small subset of those permissions. In this article I will show you how to grant an AD group permission to reset passwords and unlock user accounts using Active Directory’s Delegation of Control Wizard. Once you’re familiar with the process, you will be able to use the same wizard to delegate other tasks.
It’s preferable to create an OU structure so that you can apply different delegated permissions and Group Policy Objects (GPOs) to different sets of AD objects. For example, you may not want to give helpdesk users the ability to manage sensitive user accounts, in which case the given accounts need to be located in their own OU so that different management policies can be applied.
For the purposes of this guide, I’ll delegate permissions to objects in the standard Users container.
- Log on to Windows Server 2012 as a domain administrator and open Server Manager from the icon on the desktop Taskbar or from the Start screen.
- Select Active Directory Users and Computers (ADUC) from the Tools menu.
- In the left pane of ADUC, expand your domain, right-click the Users container (or the OU for which you want to delegate permissions) and select Delegate Control from the menu.
- Click Next on the welcome screen.
- On the Users or Groups screen, click Add.
- In the Select Users, Computers, or Groups dialog, type the name of the AD group you want to give permission to reset user account passwords and click OK. In this example, I already have an AD group called HelpDesk that I’m going to use.
- On the Users or Groups screen, click Next.
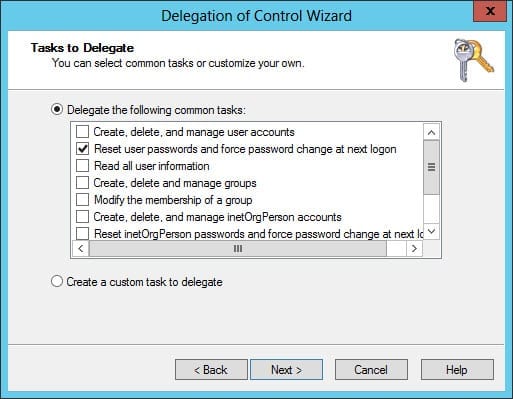
- On the Tasks to Delegate screen, check Reset user passwords and force password change at next logon and click Next.
- Click Finish.
Remember that standard users cannot log on locally to domain controllers (DCs). Even if you change this policy, standard users cannot run the Microsoft Management Console by default on DCs, hence preventing them from starting ADUC. Your IT staff should use the Remote Server Administration Tools (RSAT) to manage AD from a management workstation.