What is a VLAN? How to Setup a VLAN on a Cisco Switch
Have you ever wondered what a Virtual LAN (or VLAN) is or been unclear as to why you would want one? If so, I have been in your place at one time too. Since then, I have learned a lot about what a VLAN is and how it can help me. In this article, I will share that knowledge with you.
What is a LAN?
Okay, most of you already know what a LAN is but let’s give it a definition to make sure. We have to do this because, if you don’t know what a LAN is, you can’t understand what a VLAN is.
A LAN is a local area network and is defined as all devices in the same broadcast domain. If you remember, routers stop broadcasts, switches just forward them.
What is a VLAN?
As I said, a VLAN is a virtual LAN. In technical terms, a VLAN is a broadcast domain created by switches. Normally, it is a router creating that broadcast domain. With VLAN’s, a switch can create the broadcast domain.
This works by, you, the administrator, putting some switch ports in a VLAN other than 1, the default VLAN. All ports in a single VLAN are in a single broadcast domain.
Because switches can talk to each other, some ports on switch A can be in VLAN 10 and other ports on switch B can be in VLAN 10. Broadcasts between these devices will not be seen on any other port in any other VLAN, other than 10. However, these devices can all communicate because they are on the same VLAN. Without additional configuration, they would not be able to communicate with any other devices, not in their VLAN.
Are VLANs required?
It is important to point out that you don’t have to configure a VLAN until your network gets so large and has so much traffic that you need one. Many times, people are simply using VLAN’s because the network they are working on was already using them.
Another important fact is that, on a Cisco switch, VLAN’s are enabled by default and ALL devices are already in a VLAN. The VLAN that all devices are already in is VLAN 1. So, by default, you can just use all the ports on a switch and all devices will be able to talk to one another.
When do I need a VLAN?
You need to consider using VLAN’s in any of the following situations:
- You have more than 200 devices on your LAN
- You have a lot of broadcast traffic on your LAN
- Groups of users need more security or are being slowed down by too many broadcasts?
- Groups of users need to be on the same broadcast domain because they are running the same applications. An example would be a company that has VoIP phones. The users using the phone could be on a different VLAN, not with the regular users.
- Or, just to make a single switch into multiple virtual switches.
Why not just subnet my network?
A common question is why not just subnet the network instead of using VLAN’s? Each VLAN should be in its own subnet. The benefit that a VLAN provides over a subnetted network is that devices in different physical locations, not going back to the same router, can be on the same network. The limitation of subnetting a network with a router is that all devices on that subnet must be connected to the same switch and that switch must be connected to a port on the router.
With a VLAN, one device can be connected to one switch, another device can be connected to another switch, and those devices can still be on the same VLAN (broadcast domain).
How can devices on different VLAN’s communicate?
Devices on different VLAN’s can communicate with a router or a Layer 3 switch. As each VLAN is its own subnet, a router or Layer 3 switch must be used to route between the subnets.
What is a trunk port?
When there is a link between two switches or a router and a switch that carries the traffic of more than one VLAN, that port is a trunk port.
A trunk port must run a special trunking protocol. The protocol used would be Cisco’s proprietary Inter-switch link (ISL) or the IEEE standard 802.1q.
How do I create a VLAN?
Configuring VLAN’s can vary even between different models of Cisco switches. Your goals, no matter what the commands are, is to:
- Create the new VLAN’s
- Put each port in the proper VLAN
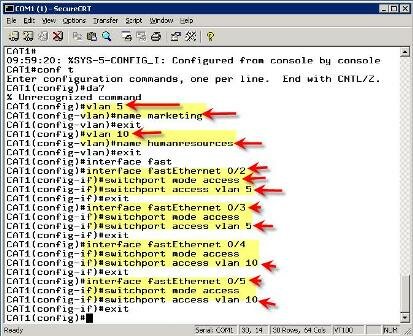
Let’s say we wanted to create VLAN’s 5 and 10. We want to put ports 2 & 3 in VLAN 5 (Marketing) and ports 4 and 5 in VLAN 10 (Human Resources). On a Cisco 2950 switch, here is how you would do it:
At this point, only ports 2 and 3 should be able to communicate with each other and ports 4 & 5 should be able to communicate. That is because each of these is in its own VLAN. For the device on port 2 to communicate with the device on port 4, you would have to configure a trunk port to a router so that it can strip off the VLAN information, route the packet, and add back the VLAN information.
What do VLAN’s offer?
VLAN’s offer higher performance for medium and large LAN’s because they limit broadcasts. As the amount of traffic and the number of devices grow, so does the number of broadcast packets. By using VLAN’s you are containing broadcasts.
VLAN’s also provide security because you are essentially putting one group of devices, in one VLAN, on their own network.
Article Summary
Here is what we have learned:
- A VLAN is a broadcast domain formed by switches
- Administrators must create the VLAN’s then assign what port goes in what VLAN, manually.
- VLAN’s provide better performance for medium and large LAN’s.
- All devices, by default, are in VLAN 1.
- A trunk port is a special port that runs ISL or 802.1q so that it can carry traffic from more than one VLAN.
- For devices in different VLAN’s to communicate, you must use a router or Layer 3 switch.
- Even if you’ve worked on Cisco networks for a while, be sure to check out TrainSignal’s CCNA training