Configure Windows Azure to Accept Point-to-Site VPN Connections
Microsoft introduced point-to-site VPN connections to Windows Azure in 2013, and they are currently available as a preview feature, allowing customers to connect individual on premise servers, or remote devices, to Azure via an SSTP VPN. In the first of this two-part series, I’ll show you how to configure Azure to accept a point-to-site VPN connection from Windows Server 2012 and other supported remote devices, so that you can access Azure resources.
What Is the Difference Between Site-to-Site and Point-to-Site VPNs in Windows Azure?
The key advantage of point-to-site VPNs is that Secure Socket Tunneling Protocol (SSTP) is used, so NAT firewalls can be traversed and a dedicated public-facing IPv4 address isn’t required. Site-to-site VPNs offer higher bandwidth connections to Azure, offer more flexibility, and use IPsec; so require a network edge router with a spare public-facing IPv4 address.
Site-to-site VPNs to Azure are always-on and don’t require any configuration of individual on premise clients or servers. They also allow bidirectional communication, so a server running on Azure can initiate a connection to a server running on an on-premise network.
Configure a Point-to-Site VPN in Windows Azure
Let’s start by configuring VPN support in the Azure management portal.
- Login to the Azure management portal.
- In the blue panel on the left, click Networks.
- Now click +NEW in the grey bar at the bottom of the portal and click Custom Create in the pop-up dialog.
- In the Create a Virtual Network dialog, give the new virtual network a name and select an affinity group from the drop-down menu.
If you don’t have an existing affinity group configured, select Create a new affinity group from the menu and give the new group a name and region.
- Click the Next arrow in the bottom right of the dialog to continue.
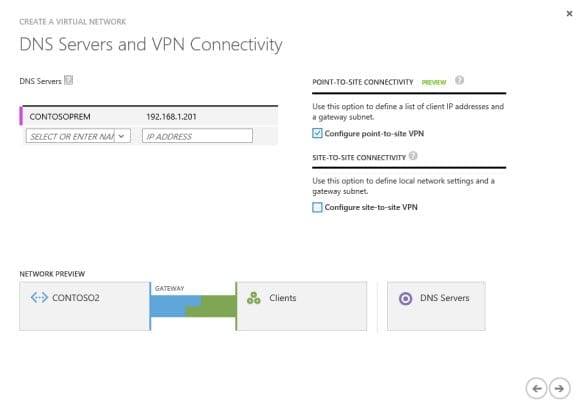
- On the DNS Servers and VPN Connectivity screen, I’m going to enter the IP address of a DNS server on my on premise network, and call it CONTOSOPREM.
- Now check Configure point-to-site VPN and click the forward arrow to continue. Notice how the network diagram changes to represent the point-to-site VPN.
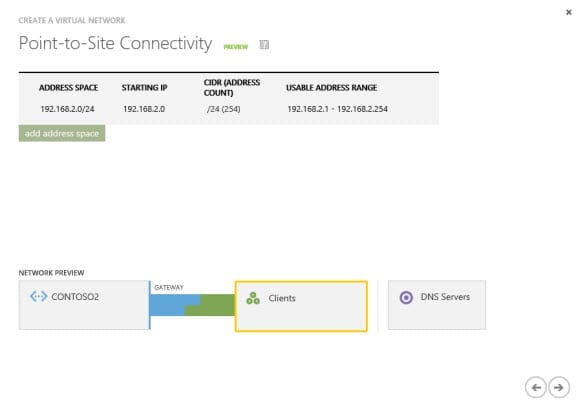
- On the Point-to-Site Connectivity screen, choose an address space from which IP addresses will be assigned to VPN clients. This address space shouldn’t overlap your on premise local network or Azure virtual network IP address ranges. For this demonstration, I have chosen 192.168.2.1/24. Click the forward arrow to continue.
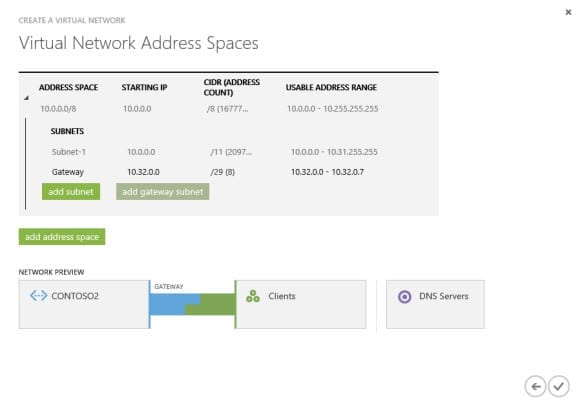
- On the Virtual Network Address Spaces screen, define the address space and subnets for your Azure virtual network. In this demo, I’ll accept the default address space of 10.0.0.0/8 and subnet 10.0.0.0/11. The address space for the Azure virtual network must be private, and cannot overlap other virtual networks or local network sites.
- Staying on the Virtual Network Address Spaces screen, click the green add gateway subnet button. Again, I’ll accept the default gateway subnet of 10.32.0.0/29.
- To complete the procedure, click the tick icon on the bottom right of the dialog.
- You’ll see the new virtual network in the list. Click it.
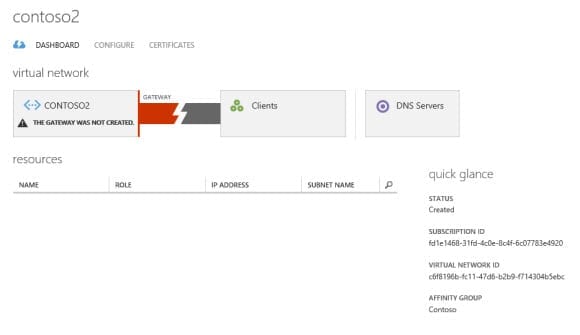
- On the virtual network’s screen, switch to the Dashboard tab.
- You’ll see an error alert in the network diagram, stating that THE GATEWAY WAS NOT CREATED. To fix this, click Create Gateway at the bottom of the portal.
- In the pop-up dialog, confirm that you want to create a gateway for the virtual network by clicking Yes.
Note that this process can take between 10 and 15 minutes to complete. Once the gateway has been created, the network diagram on the dashboard will change, and you’ll see an alert stating that a root certificate has not been uploaded.
Create a Root Self-Signed Certificate
Before we can make a connection between our on premise server and Windows Azure, we need to create a self-signed root certificate for the VPN. While point-to-site VPNs are in preview, only self-signed certificates are supported.
- To get the latest version of makecert, run the web installer for the Windows SDK.
- On the Specify Location screen, accept the default install location and click Next.
- Click Next past the Join the Customer Experience Improvement Program screen.
- Click Accept on the License Agreement screen.
- On the Select the features you want to install screen, uncheck everything except Windows Software Development Kit and click Install.
- Close the installer window once the download has completed.
- You’ll find the makecert.exe tool in the C:\Program Files (x86)\Windows Kits\8.1\bin\x64 and x86 folders.
- Open a command prompt in the directory where you want to save your certificates. makecert.exe should be located in the same directory. To open a command prompt, right-click the directory folder while holding SHIFT, and select Open command window here from the menu.
- In the command prompt window, type makecert -sky exchange -r -n “CN=CONTOSO2” –pe -a sha1 -len 2048 -ss My and press Enter, replacing the certificate name (CN) with something appropriate for your Azure virtual network. This command will generate a certificate in the Personal certificate store of your user account.
- Now let’s export the certificate. Switch to the Start menu and type mmc. Click MMC in the search results.
- In the MMC window, click File and select Add/Remove Snap-in from the menu.
- In the Add or Remove Snap-ins window, select Certificates under Available snap-ins, click Add and then OK.
- In the MMC window, expand Certificates – Current User, Personal, Certificates in the left pane.
- Right-click the certificate created by makecert in the center pane and select All Tasks, Export from the menu.
- In the Certificate Export Wizard, click Next on the welcome screen.
- On the Export Private Key screen, select No, do not export the private key and click Next.
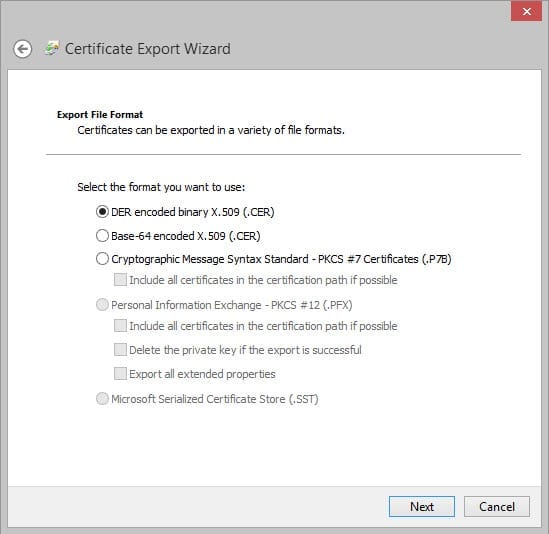
- On the Export File Format screen, check DER encoded binary X.509 (.CER) and click Next.
- On the File to Export screen, click Browse and save the certificate to your working directory for makecert. Make sure the file has the .cer file extension. Click Next to continue.
- Click Finish to complete the process.
In part two of this series, we’ll create another certificate for the VPN client and then download the VPN software and install it on our on premise server before testing the connection.



