Configure DNS to Enable a Trust Between Two Active Directory Forests
Before you can create a cross-forest trust in Active Directory, DNS name resolution needs to be working between the two forests. In today’s Ask the Admin, I’ll show you how to set up DNS in Windows Server so that you can establish a cross-forest trust.
A robust DNS infrastructure is critical for a healthy Active Directory. DNS can be automatically set up and configured when you install a domain controller. But when you need to create a trust between two AD forests, you will have to perform some manual configuration in DNS to ensure that name resolution works between the two forests.
Secondary Zones and Delegation
There are different ways to set up name resolution between two DNS domains. One is creating a secondary zone on your DNS server. A secondary zone contains a complete copy of a DNS zone from another DNS server. For example, I could create a secondary zone for pim.contoso.com on a DNS server running in the ad.contoso.com domain.
Delegation allows a domain’s root DNS server to resolve queries for subdomains. When creating a delegation, you specify the subdomain to delegate and the IP address or fully-qualified domain name (FQDN) of the DNS server that will host the delegated zone. For instance, a root DNS server hosting contoso.com could delegate DNS for ad.contoso.com to another DNS server.
Stub Zones and Forwarding
Stub zones are copies like secondary zones but contain just Name Server (NS), Start of Authority (SOA), and sometimes glue Host (A) records because stub zones are not authoritative for the domain. Unlike delegation, stub zones can be copies of zones from any domain. For instance, you could create a stub zone for pim.contoso.com on a server in the ad.contoso.com domain. The authoritative DNS server for pim.contoso.com must give permission for the partial zone transfer to the ad.contoso.com DNS server.
DNS forwarders can be used to redirect lookup queries to another DNS server. In Windows Server DNS, you can configure a forwarder to send all queries that cannot be resolved by the local DNS server to another server. In addition to that, Windows Server DNS supports conditional forwarding, which sends lookup queries for a domain to another server without attempting to resolve the query locally.
Root Hints
Root hints are similar to forwarders but use iterative queries instead of recursive queries. Recursive queries are passed to a name server listed in the forwarder configuration and the client waits for an answer. Recursive queries can supply the client with a referral that requires it to query another name server. This process continues until an answer is provided. Recursive queries are more resource intensive for the client.
Set Up Conditional Forwarding
So which method should you use when configuring DNS name resolution for establishing a trust between two Active Directory forests? The most efficient way to resolve names in pim.contoso.com from ad.contoso.com, and vice versa, is to set up a conditional forwarder in both forests. There is no DNS root server that can be the server for both DNS domains, so delegation cannot be used.
Conditional forwarders are best suited in situations where we know that the IP addresses of authoritative DNS servers are not going to change often. Stub zones are better when authoritative DNS servers frequently change because stub zones do not usually require manual reconfiguration. Conditional forwarders provide non-authoritative responses because the zones are not hosted on the DNS server against which the queries are made. But in a secured AD environment that is OK.
It is worth noting that if you had Preferred DNS server and Alternate DNS server IP addresses set in the client list of IP addresses for the server before it was promoted to a domain controller and they were something other than the server’s own IP address those addresses are automatically added to the DNS server’s Forwarders list when DNS is installed. This configuration is not automated on servers that are multihomed. I.e. servers that are connected to more than one network.
The quickest way to create a conditional forwarder on your DNS server is using PowerShell. Log into the DNS server, open a PowerShell window, and run the command below. In this example, I am logging into ad.contoso.com and want to set up a conditional forwarder for the pim.contoso.com domain. I know the DNS server IP address in the pim.contoso.com domain is 192.168.1.2.
Add-DnsServerConditionalForwarderZone -Name pim.contoso.com -MasterServers 192.168.1.2
I can then repeat this action in the pim.contoso.com forest and set up a conditional forwarder for the ad.contoso.com domain:
Add-DnsServerConditionalForwarderZone -Name ad.contoso.com -MasterServers 192.168.1.1
My AD forests each have one domain controller and one DNS server. If you have more than one DNS server in a domain or forest, you can configure forwarders to be replicated in AD by adding the -ReplicationScope parameter and setting the value to Forest or Domain.
If you want to configure a DNS conditional forwarder using the GUI, here is how to do it in Windows Server 2016:
- Log into the DNS server.
- Open Server Manager from the Start menu.
- In Server Manager, select DNS from the Tools menu.
- Expand the DNS server tree in the left pane, right-click Conditional Forwarders and select New Conditional Forwarder from the menu.
- In the New Conditional Forwarder window, type the name of the DNS domain for which you want to resolve queries.
- In the list of IP addresses, click <Click here to add an IP Address or DNS Name>.
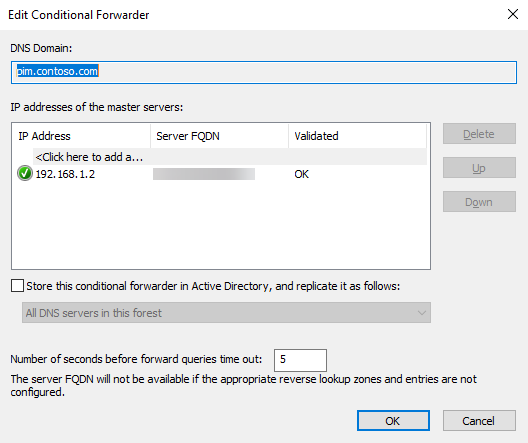
- Type the IP address of the DNS server that will resolve queries from the domain you entered in the previous step and press ENTER.
- If the DNS server can be reached, after a few seconds the Server FQDN name field will display the name of the DNS server.
- If you want to replicate the conditional forwarder in AD, click Store this conditional forwarder in Active Directory, and replicate it as follows:
- Select All DNS servers in this forest or All DNS servers in this domain from the drop-down menu.
- Click OK.
Do not worry if the DNS server you enter for the conditional forwarder is not validated at first. Wait a few minutes and check the properties of the conditional forwarder again. You should see that the server has been validated.
In this Ask the Admin, I showed you the best way to set up DNS name resolution between two Active Directory forests.




