Protecting Office 365 Documents with Conditional Access Policies
Better Protection for Office 365
Having technology that can do one thing well is goodness. Combining that technology with other technology to do more is even better, which is what Microsoft is doing with the preview of Conditional Access for Azure Information Protection (AIP).
Labels Documents Containing Sensitive Information
AIP is one of the multiple ways to label information within Office 365. Thankfully, Microsoft has embarked on a plan to bring classification labels (as used in data governance) and AIP labels together to create a label to rule them all. For now, we operate on the basis that users apply AIP labels through the Office applications (Figure 1) to mark documents and messages with different levels of sensitivity. For the most sensitive material, AIP labels can invoke protection templates to restrict what recipients can do with information.
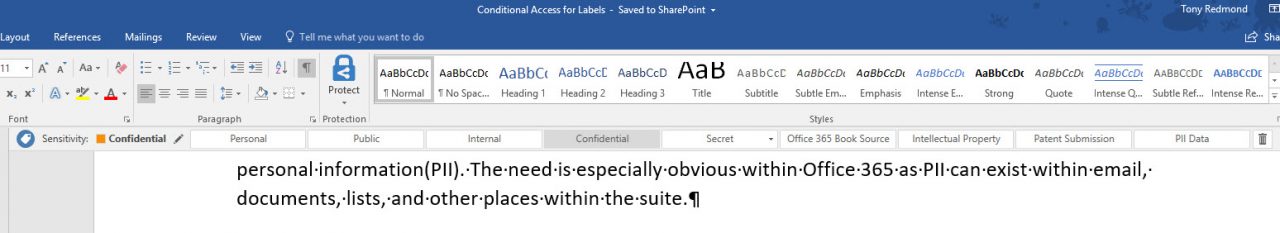
A classified document is a Word, Excel, or PowerPoint file stamped with an AIP label. Users can also apply AIP labels to email through Outlook.
Conditional Access and Office 365
Conditional access policies are an Azure Active Directory premium feature to control the access users have to applications running in your environment. Multiple access policies allow fine-grained control over who can access what and when, if that is how you want access to work. As explained here, when a user is subject to a conditional access policy, Azure AD redirects their request to Microsoft Cloud App Security proxy to evaluate and decide whether access is allowed under current conditions.
The Office 365 applications that support conditional access are:
- Exchange Online.
- SharePoint Online.
- Teams.
- Yammer.
You need to pay attention to conditional policies that control access to Exchange Online and SharePoint Online to ensure that applications which depend on these workloads, like Teams, work. Also, users who come within the scope of conditional policies need Azure Active Directory Premium P1 licenses. See the FAQ for more information.
Better Protection for Confidential Information
Based on the number of mentions during Ignite sessions, the advent of the European Union General Data Protection Regulation (GDPR) in May 2018 has focused minds on how to protect and secure personal information (PII). The need is especially obvious within Office 365 as PII can exist within email, documents, lists, and other places within the suite.
Office 365 already has technologies to help control the misuse of PII, including DLP, classification labels, rights management, and so on. The question I had was whether conditional access linked to AIP would help.
AIP-classified documents stamped with a label that invokes a protection template already enjoy substantial protection. These documents can only be opened by people who have the rights to do so, and those people can only use their assigned rights to interact with the content. For example, the template assigned to a document might stop recipients being able to print the document or copy text from the document. You can assign rights to people outside your organization and can revoke those rights at any time should the need arise.
On the other hand, documents classified with a lower-sensitivity label might not have the same protection and their content is therefore accessible by anyone who receives a copy. These documents might contain PII data, and this is where I see the value of conditional access because you can implement a policy to restrict access to classified documents unless certain conditions exist. The examples cited by Microsoft include requiring the use of multi-factor authentication (MFA), restrict access to domain-joined devices, block risky sign-ins, and limit devices to those coming from a trusted network.
Defining a Policy
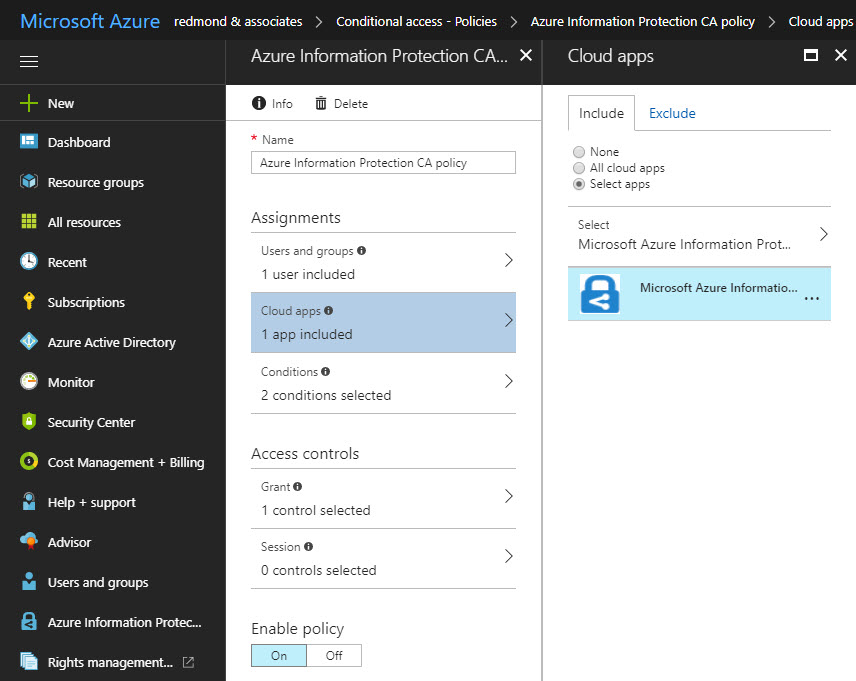
Defining a new conditional access policy is easy. Go to the Azure Active Directory section of the portal (or blade, in Microsoft terminology), select Conditional access under Security, and then New policy. Policy settings include:
- The users and groups to whom the policy applies.
- The cloud apps within scope (in this case, it is only Azure Information Protection).
- The conditions to invoke the policy.
- The access controls.
I followed the steps laid out by Microsoft to create a policy to require users to authenticate with MFA when accessing classified material using browsers and desktop clients on Windows (you can also select Android, iOS, Windows Phone, and Mac OS). Creating the policy (Figure 2) took less than five minutes. To make it effective, you enable and save the policy to force Azure Active Directory to apply conditional access.
Users and MFA
The effect is most obvious for accounts that are not enabled for MFA as they cannot access classified documents until they go through the MFA challenge process. Conditional access uses per-app challenges, which means that the challenge is valid for access for whatever app or apps associated with a policy.
In this case, that app is Azure Information Protection and the access token granted through the challenge is valid for any application that use AIP to protect documents for up to an hour. In other words, you do not have to authenticate again if you open a Word document followed by an Excel spreadsheet within the lifetime of the access token (you can configure the token lifetime to last longer).
Office 365 accounts enabled for MFA notice no difference because they already authenticate using MFA. If you deploy a conditional access policy for AIP that requires MFA, it makes sense to enable tenant accounts for MFA so that users authenticate once when they access Office 365.
The point here is that if someone gets hold of a copy of a classified document, spreadsheet, or presentation that holds some sensitive information, they cannot open it unless they can authenticate with your domain using MFA. Failure means that the documents are useless. Which is, I guess, what conditional access is all about.
Flexible Conditions
You might not want an MFA challenge to occur every time a tenant user opens a classified document. Fortunately, you can specify different conditions to control how the policy applies. For instance, you can define that the policy only applies when certain users connect from named locations (IP address ranges). Conditional policies are flexible enough to deal with different circumstances, even if it might take you some trial and error to arrive at the right combination to meet your needs.
Not for Everyone
Like everything in the Microsoft cloud ecosystem, conditional access policies and Azure Information Protection are tools that might or might not make sense in your environment. But if they do, it’s nice to be able to mix and match technologies to get better protection.
Follow Tony on Twitter @12Knocksinna.
Want to know more about how to manage Office 365? Find what you need to know in “Office 365 for IT Pros”, the most comprehensive eBook covering all aspects of Office 365. Available in PDF and EPUB formats (suitable for iBooks) or for Amazon Kindle.
Related Article:




