Azure Update Management Part 2: Schedule Updates, Check Update Compliance, and Enroll Non-Azure VMs
In the first part of this series, I showed you how to enroll Azure virtual machines to Azure Update Management. In the final part, I’ll demonstrate scheduling updates, checking update compliance, and how to enable Update Management on non-Azure VMs.
Schedule Updates
You can create a specific schedule for updates on each VM that is enrolled with Azure Update Management. If a VM is configured to use WSUS, those settings will always take precedence over any deployment schedule configured in Azure Update Management.
To create a new deployment schedule:
- In Update Management in the Azure management portal, click Schedule update deployment.
- In the New update deployment pane, give the new deployment a name.
- You can choose to exclude certain update categories, like security updates and service packs. You can also exclude specific updates by providing their Knowledge Base IDs.
- Finally, you must provide schedule settings. A time and start date. The schedule can be one time only or recurring. If you set a recurring schedule, you can set the frequency and set an expiration date.
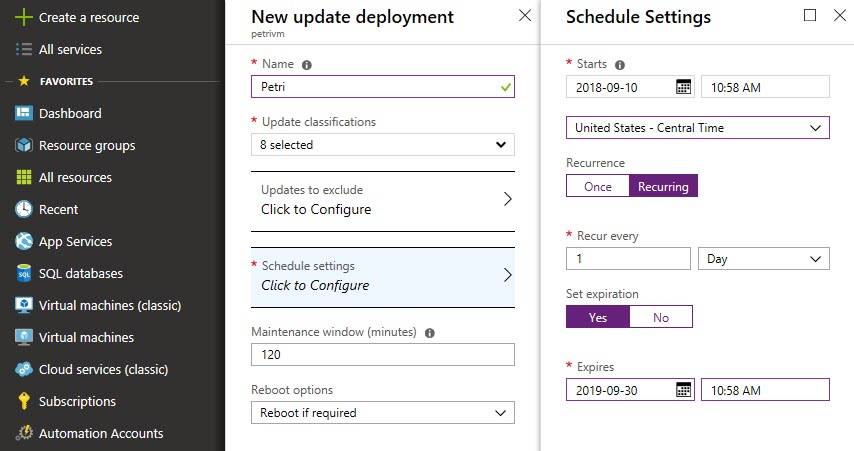
- The standard maintenance window is set to 2 hours. The last 20 minutes of which is reserved for rebooting the server. The minimum maintenance window is 30 minutes. Any updates that have not been started by the time the maintenance window is over will be skipped. If updates are already in progress, they will be completed.
- The reboot options allow you to reboot the server if required or set it to never reboot.
- Click Create when you are done configuring the deployment settings.
Checking Update Compliance
You can use Azure Update Management to check update compliance. Scans are performed every 12 hours by default on Windows servers (3 hours on Linux servers) and the agent sends the results to Azure Log Analytics. Scans for update compliance are performed within 15 minutes after the MMA service starts, before update installation, and after update installation.
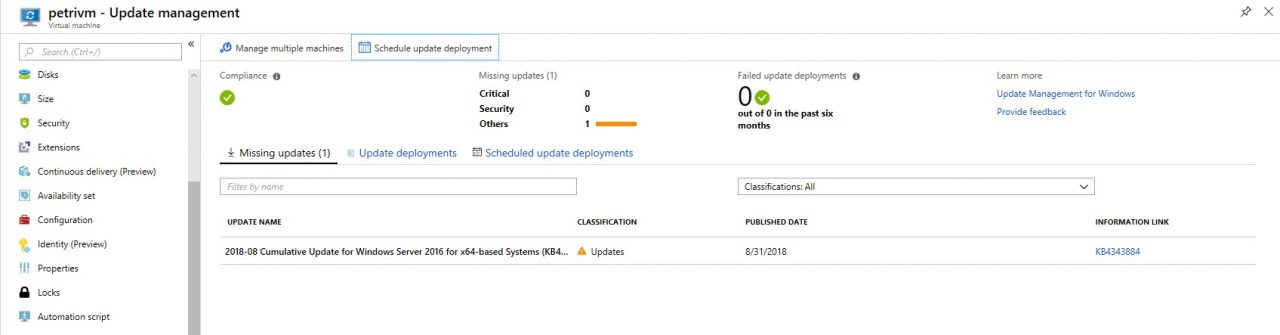
To view compliance for a single VM:
- In the Azure management portal, click Virtual machines in the list of options on the right.
- Select a virtual machine from the list on the right for which you’d like to check update compliance.
- In the list of options for the VM, scroll down to Operations and click Update management.
- On the Update management pane, click Missing updates if it’s not already selected. Here you’ll see a list of missing updates.
- On the Update management pane, you can also see any update deployments that are currently in progress or those that are scheduled to run in the future.
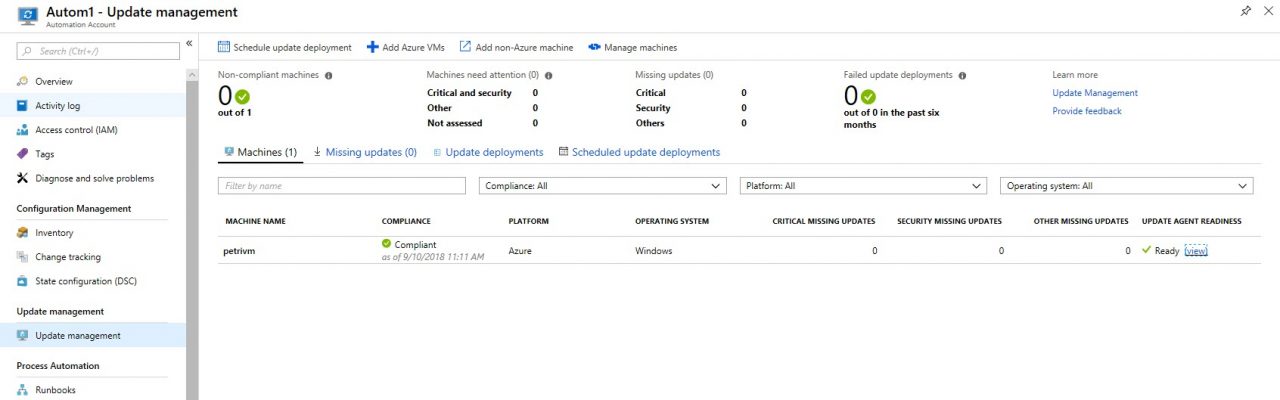
To view compliance for all VMs enrolled with an automation account:
- In the Azure management portal, select Automation Accounts in the list of options on the left.
- In the list of automation accounts, click the account you chose to use when configuring Update Management.
- On the automation account pane, click Update Management in the list of options on the left.
- Now you can see a list of all the VMs enabled for Update Management and an overview of machines that need attention and of missing updates.
Enable Update Management on non-Azure VMs
Finally, to enable Azure Update Management on VMs that aren’t hosted in Azure you need to manually install and configure the Microsoft Monitoring Agent. The only requirement is that VMs are running a supported version of Windows Server or Linux and that they have Internet connectivity. More specifically, VMs must be able to communicate with the following addresses over port 443: *.ods.opinsights.azure.com, *.oms.opinsights.azure.com, and *.blob.core.windows.net.
For instructions on how to install the MMA manually, see Aidan Finn’s article On-Premises Deployment of Azure Log Analytics (OMS) on Petri.
In this article, I showed you how to schedule updates and check update compliance using Azure Update Management.




