Advanced Office 365 Message Encryption Includes Branded Communications and Revocation
Message Encryption for the Office 365 Masses
Office 365 Message Encryption (OME) is the technology behind the ability of Exchange Online users to send encrypted messages sent to any recipient. Included in the Office 365 E3 and E5 plans (and equivalent education and government plans), OME is automatically enabled for tenants to allow people to use the Encrypt-Only feature supported by Outlook and OWA. Outlook mobile can read encrypted email inline but isn’t yet able to send encrypted messages. To support clients that don’t support encryption, OME also supports encryption through Exchange transport rules (aka mail flow rules).
Advanced OME adds three features to the standard OME functionality:
- Branding, so that recipients in specific email domains see instructions (to access the messages) in custom templates.
- Message expiration, so that messages sent using custom branding expire after a set period.
- Revocation, the ability to withdraw an encrypted message sent to external recipients.
Advanced OME is available in the Office 365 E5 plan and as part of the Office 365 Advanced Compliance add-on (SKU).
Creating Branding Templates
When you send an encrypted message from Office 365, the protected content is inside a “wrapper” and an RPMSG, or “restricted permission” attachment holds the encrypted content. The wrapper is a notification to the recipient to tell them how to access the protected content via the OME portal.
Clients like OWA, Outlook, and Outlook mobile know to process these messages by stripping the wrapper and decrypting the enclosed content to display it like normal messages. This happens automatically for recipients inside the same Office 365 tenant, if they use an Outlook client. External recipients see the notification message. These recipients are called link-based recipients. The text and graphic elements of the notification are controlled by settings in the OME configuration.
Standard OME has a single configuration (standard template) applied to outbound encrypted messages. Advanced OME adds the ability to create new configurations, each of which includes properties to build different elements of the branding you want to apply to messages.
Working with OME Configurations
OME configurations are created and updated through PowerShell using the New-OMEConfiguration, Get-OMEConfiguration and Set-OMEConfiguration cmdlets. The settings for the standard configuration are accessed by running:
Get-OMEConfiguration -Identity "OME Configuration”
To create a new branding configuration for use with a specific domain, run the New-OMEConfiguration cmdlet:
New-OMEConfiguration -Identity "Office 365 IT Pros"
You then use the Set-OMEConfiguration cmdlet to update the configuration to tweak different aspects of the notification message created using the template such as the image in the notification heading (shown instead of the Office 365 logo) and text displayed in different places in the message. For example, this command sets four different text strings, adds a different picture, and sets a 10-day expiration period for any message sent using the template. The picture should be no more than 170 x 170 pixels.
Set-OMEConfiguration -Identity "Office 365 IT Pros" -DisclaimerText "Office 365 for IT Pros takes no responsibility for this portal." -PortalText "Office 365 for IT Pros Secure Messaging" -EmailText "Good things happen when you protect email" -ExternalMailExpiryInDays 10 -IntroductionText "has sent you a secret message" -Image (Get-Content "C:\Temp\SmallBookCover.jpg" -Encoding byte)
Applying Branded Templates
The standard OME configuration applies to any encrypted message leaving the tenant. To apply the branded template, we create a transport rule to look for any messages going to a specific domain and encrypt the message and apply the template to matching messages. Applying encryption through a transport rule in Exchange Online means that users with on-premises mailboxes in hybrid organizations can benefit from OME.
Custom branding is only applied when messages are processed by a transport rule. This applies no matter how a message is encrypted – by a transport rule, by a client applying a rights management template to protect a message, or when an Office 365 Data Loss Prevention policy encrypts messages containing sensitive data.
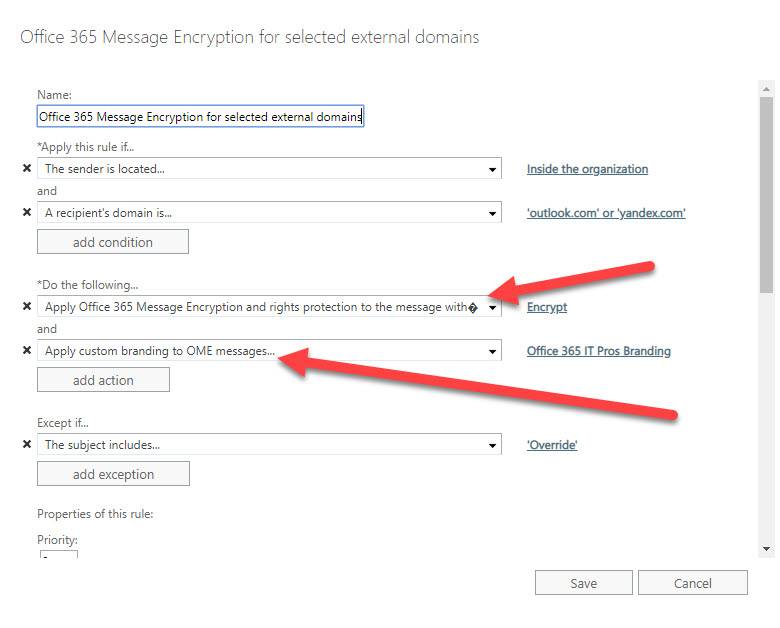
Figure 1 shows the kind of transport rule we need. The rule applies to any message sent from inside the organization to two named domains. If invoked, the rule applies two actions. First, it encrypts the message. Second, it applies custom branding.
Testing a Branding Template
To test the template, send an encrypted message to one of the target domains. In our case, the two domains are Outlook.com and Yandex.com. Figure 2 shows the result of branding for a message delivered to a Yandex.com recipient. The changed strings are obvious as is the custom logo.
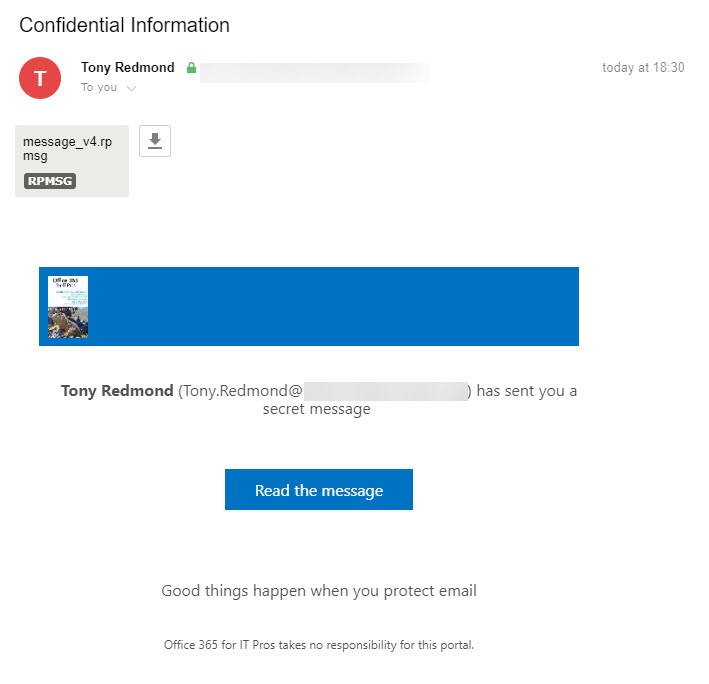
The link to the encrypted content is accessed via the Read the message button. You can change this text by updating the ReadButtonText property in the OME configuration.
Revocation
Revocation is only possible for external recipients who receive link-based notifications. To revoke a message, you can use PowerShell (the Set-OMEMessageRevocation cmdlet), or select the message from the Message encryption report in the Security and Compliance Center and revoke it there.
One thing to note is that Office 365 updates the data displayed in the message encryption report daily, so recent messages aren’t listed. If you need to revoke a message sooner, you should run a message trace to find its message identifier and then input that identifier to revoke the message with Set-OMEMessageRevocation.
When a message is revoked, the recipient is no longer able to open it.
Guest Accounts, Revocation, and Expiration
One interesting fact about message revocation is that you can’t revoke or expire a message sent to an external recipient who has a guest user account in your tenant. Setting up a guest account makes the recipient a trusted party for OME, just like tenant users, and Microsoft doesn’t support revocation to internal recipients.
I think this is odd. Guest accounts don’t show up in the GAL, so there’s no way for a normal user to know that an external recipient has a guest account. As far as a user knows, the guest account they sent an encrypted message to is like any other external recipient and no good reason exists why they should not be able to revoke that message. But they can’t. Perhaps Microsoft will consider changing this approach in a future release.
On the upside, because OME treats guest accounts as internal recipients, it means that you can allow external recipients to decrypt content automatically by creating a guest account for their email address in your tenant. There’s always a silver lining.
Advanced OME Isn’t for Everyone
Most Office 365 tenants will be happy with the features in standard OME. Those who need added control over branding for specific domains will like the flexibility of being able to customize the appearance of notification messages sent to targeted domains. Expiring confidential messages is also a nice feature for Office 365 E5 tenants to have, but I wish that message revocation was available in Office 365 E3.



