Georgia Institute of Technology security researchers released a thunderclap this week when they announced their successfully infecting iOS devices with malware. This news is obviously disturbing – not just because it shatters the misplaced ideal that iPhones and iPads are ultra-secure and exempt from such threats, but because it exposes a much deeper issue. Malware is evolving, and IT pros need to be ready.
iOS Malware: Unexpected Attacks
The researchers – Billy Lau, Yeongjin Jang, and Chengyu Song – successfully attacked the iPhone, but not by overcoming its defenses. They did it by completely ignoring them. In the Art of War, Sun Tzu famously gives this advice about confronting a secure enemy: “Attack him where he is unprepared, appear where you are not expected.” This is exactly how the team easily infected the iPhone with their “arbitrary” software.
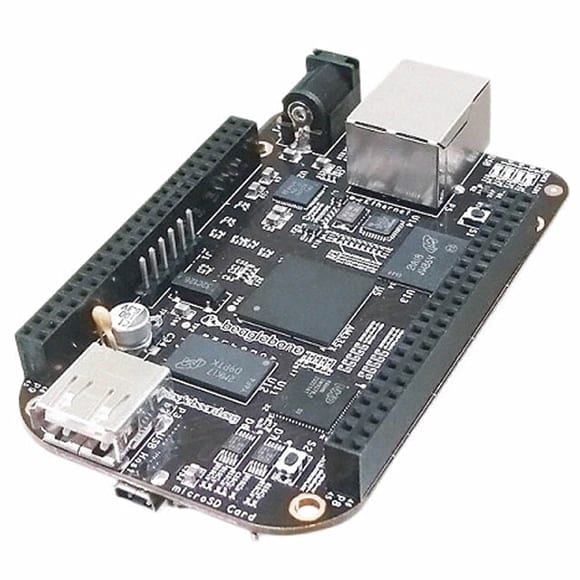
Using a specially designed USB charger allowed the team to infect an iPhone within a minute of its being plugged in. The uploaded malicious software was hidden from the user in much the same way Apple’s built-in apps are hidden. The iPhone was not modified in any way, meaning it was not jailbroken. The latest 6.x version of iOS was installed. The bottom line is that in less than 60 seconds – without any alerts, user action, or fanfare – arbitrary code was installed and hidden on the iPhone. The charger was built from the credit card-sized, low-cost, open-source BeagleBoard. This charger wasn’t meant to be pretty or mass produced. It was designed solely to prove a point.
Researchers at the Georgia Institute of Technology created a malware-laden iOS charging device by using an open-source Beagleboard.
The IT Elephant in the Room
I’m not bothered by the fact iDevices have been compromised. Regardless of opinion, it was only a matter of time. In fact, forget about iAnything for a moment – it’s a tiny animal compared to the elephant that just burst into the room. Do you see it? These researchers just turned a charger – a device no one gives any thought to – into an infection route for malware. Most of us have dozens of chargers in our house for even more devices, many of which are using the USB specification for their interfaces. I am not saying every device is prone to this type of attack. However, some surely are, and this should concern everyone in IT.
We’ve trained our users to avoid opening email attachments with any scent of oddity about them. We’ve implemented antivirus and anti-malware from our network infrastructure to our portable devices. We’ve restricted how portable drives are used. All this was done to prevent the possibility of malware infection. But has anyone ever restricted the chargers or USB cables being plugged into surge bars throughout their organizations?
Every day users bring chargers from home for one device or another. Every day users loan chargers to a coworker who might have forgotten theirs. Every day the devices using these chargers are connecting to wireless networks and other devices. Is the elephant jumping up and down yet?
Spreading the Infection
Consider a user who wants an extra charger for their company-issued iPhone. They purchase the cheapest one they can find on the Internet. The charger infects their iPhone the first time it’s plugged in. It then also infects their spouses and kid’s iPhones and iPads when those devices subsequently get plugged in for some battery refreshment. Now a half-dozen infected iDevices are on the loose!
What happens when the infectious device is plugged into the car’s USB interface on the commute to work so a few tunes can be played? Or when Bluetooth is used to connect to other devices for information sharing? Or what happens when it connects to the secure wireless network at the office? Every connection the device makes is an opportunity for its infection to spread. An opportunity every malware coder will look to take advantage of.
Staying Vigilant
Malware is not at the stage of being able to infect automobile computers through an audio interface. Nor is it ready to infect HVAC systems and the like just because an iPhone connects to network. My analogy isn’t meant to imply otherwise. My goal is to inspire all of us to begin considering the potential of malware to be more than a simple annoyance. Consider how technology proliferation has impacted daily activities and then how those technologies could be infected by malware. The first step in overcoming an enemy is acknowledging their potential to do harm.
This development doesn’t scare me – in fact, quite the opposite. It motivates me. I’m reminded that technology is a critical component of commerce, health care, communication, transportation, and just about everything else. I have a responsibility as an IT professional to apply my expertise to prevent these technologies from being disrupted or misused used by malware. I must think outside of the box. It requires that I be proactive instead of only reactive.
More than ever, malware is a virulent disease. It infects our technology, but more importantly, it cripples our lives. It impacts everything from our communications to our commutes. Malware doesn’t care about borders, age, language, or social status. Like any disease, malware doesn’t concern itself with casualties. It will cripple any system and disable the flow of information at every opportunity.
Malware will continue to try and appear where we don’t expect it. That’s all right. IT professionals will work harder than ever to be standing there, ready and waiting, when it next tries to sneak in through the back door.